Articles
Tutorials
Interactive Guides
Snyk Bitbucket pipelines integration to achieve DevSecOps

Simon Maple
Field CTO at Snyk
Achieve DevSecOps by integrating Snyk with Bitbucket Pipelines and Jira.
Time
5-minute read.
Audience
Developers, security/application teams, and DevOps/DevSecOps engineers.
Prerequisites
You have a Snyk account. Get started here.
You have an Atlassian Bitbucket account. Log in here, or get started here.
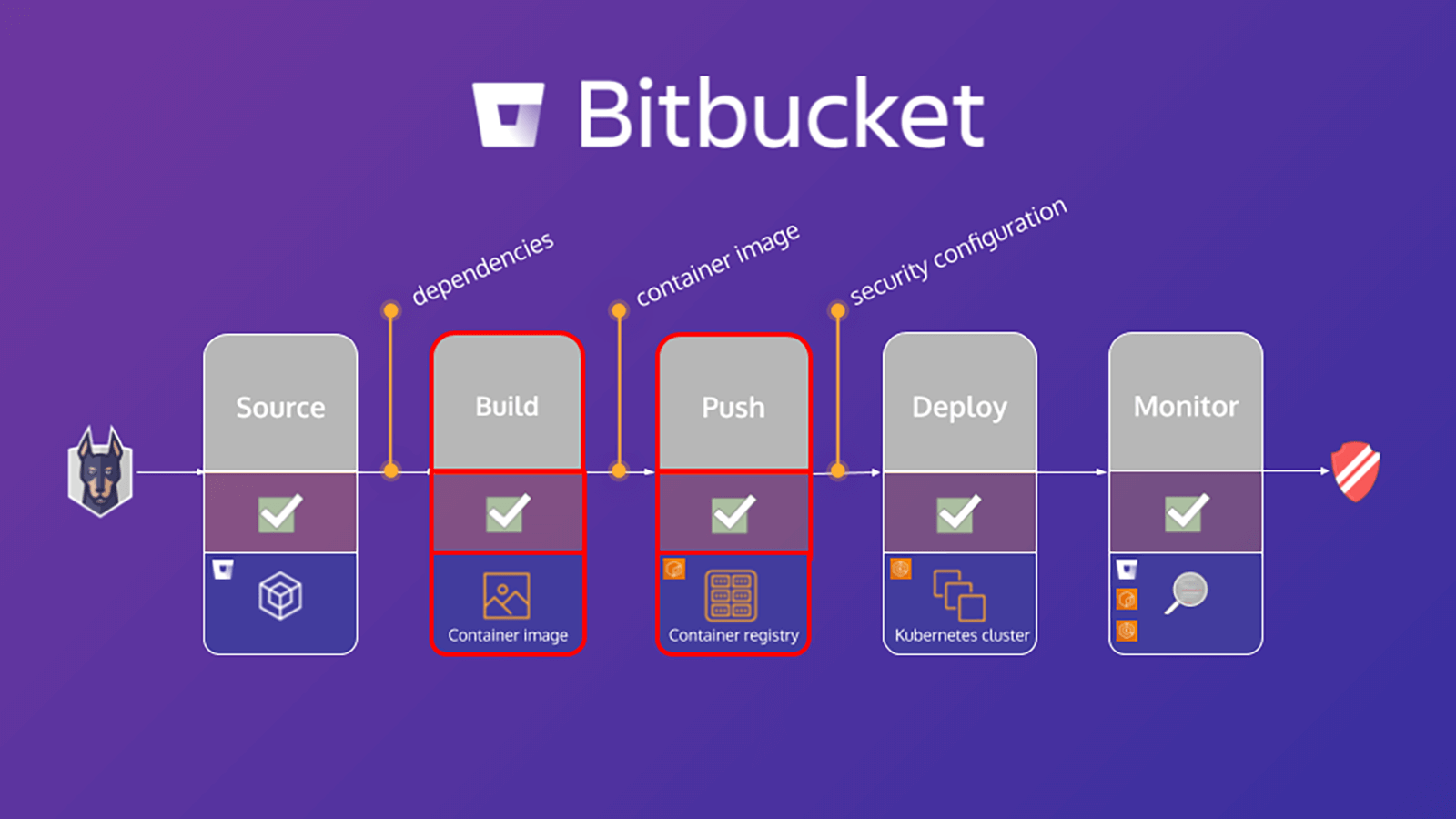
This tutorial outlines how to secure your build workflow on Bitbucket Pipelines with Snyk. An important step in securing your environment is to scan and analyze both your application and Linux-based container project for known vulnerabilities, which helps you identify and mitigate security vulnerabilities. The exercises in this tutorial will help secure your application and container by leveraging the Snyk Pipe for Bitbucket Pipelines to scan the application manifest file and the container base image for its dependencies.
The tutorial, How Snyk and Bitbucket Cloud enable DevSecOps, focused on application dependencies. However, by also scanning your container base image you can detect:
- The operating system (OS) packages installed and managed by the package manager
- Key binaries —layers that were not installed through the package manager
Based on these results, Snyk provides advice and guidance, including:
- Origins of the vulnerabilities in OS packages and key binaries
- Base image upgrade details or a recommendation to rebuild the image
- Dockerfile layer where the affected package was introduced
- Fixed-in version of the operating system and key binary packages
Application scanning in your Bitbucket Pipeline
The bitbucket-pipelines.yml file defines your Bitbucket Pipelines builds configuration. If you're new to Bitbucket Pipelines you can learn more about how to get started here.
This tutorial provides a sample bitbucket-pipelines.yml file that contains distinct steps mapped to the workflow. We’ll start by scanning the application, building the Docker image, and then scanning the container image. The following is a closer look at the application scanning step:
scan-app: &scan-app
- step:
name: "Scan open source dependencies"
caches:
- node
script:
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "npm"
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "package.json"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"This example leverages the Snyk Scan pipe in the pipeline to perform a scan of the application. The source contains a complete, YAML definition of all supported variables, but only those included in this snippet are necessary for this purpose.
Here’s a closer look at a few of these:
1. SNYK_TOKEN is passed into the pipe as a repository variable previously defined in the [Bitbucket Configuration] module.
2. PROJECT_FOLDER is the folder where the project resides and normally defaults to. However, in this example, we set this to app/goof and pass this as an artifact to other steps in ther pipeline.
3. CODE_INSIGHTS_RESULTS defaults to false. However, since we want to create a Code Insight report with Snyk test results, set this to true.
4. SEVERITY_THRESHOLD reports on issues equal or higher to the provided level. The default is low. But in this case, we are interested only in high, so we defined this variable accordingly.
5. The DONT_BREAK_BUILD default is false, which is expected. Under normal circumstances, you would want to break the build if issues are found. However, for the purpose of this learning exercise, set this to true.
You can run Snyk security scans on your pull requests and view results in Code Insights with the help of the new Snyk Security Connect App on the Atlassian Marketplace. It's easy to get started and you can install the app with just a few clicks.
Scan the container images
By 2022, more than 75 percent of global organizations will run containerized applications in production (Gartner). Alongside widespread adoption, there has been a surge in container vulnerabilities, with a four-times increase in reported operating system vulnerabilities in 2018. And yet 80 percent of developers say they don’t test their container images during development. They either say it’s not their responsibility or they are accustomed to someone down the road catching issues, which makes scaling container security a challenge for fast-growing businesses.
Container image scanning in your pipeline
Similar to the previous section on Application Scanning, this section focuses on configuring the bitbucket-pipelines.yml file to build the Docker image for the application, scan the image, then push that image to the registry. The following is a closer look at the container image scanning step:
scan-push-image: &scan-push-image
- step:
name: "Scan and push container image"
services:
- docker
script:
- docker build -t $IMAGE ./app/goof/
- docker tag $IMAGE $IMAGE:${BITBUCKET_COMMIT}
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "docker"
IMAGE_NAME: $IMAGE
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "Dockerfile"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"This is building the container image and tagging it, then leveraging the Snyk Scan pipe in the pipeline to perform a scan of the container image. Keep the same values for CODE_INSIGHTS_RESULTS, SEVERITY_THRESHOLD and DONT_BREAK_BUILD. This also passes a few additional supported variables relevant for the Snyk Pipe in order to understand the request for a container image scan instead of an application scan. These are namely setting LANGUAGE to docker, declaring the IMAGE_NAME, and passing the appropriate repository variable, as well as setting the TARGET_FILE to Dockerfile.
Your pipeline now scans the container image for known vulnerabilities, as well as your application code.
Share this article
Next Topic
Recommended reading
Bookmark these resources to learn about types of DevOps teams, or for ongoing updates about DevOps at Atlassian.

DevOps community
DevOps learning path