Integração do Snyk com o Bitbucket Pipelines para alcançar DevSecOps

Simon Maple
CTO de campo na Snyk
Obtenha o DevSecOps integrando o Snyk com o Bitbucket Pipelines e o Jira.
Tempo
5 minutos de leitura.
Público-alvo:
Desenvolvedores, equipes de segurança/aplicativos e engenheiros de DevOps/DevSecOps.
Pré-requisitos
Você tem uma conta do Snyk. Comece aqui.
Você tem uma conta do Atlassian Bitbucket. Entre aqui ou comece aqui.
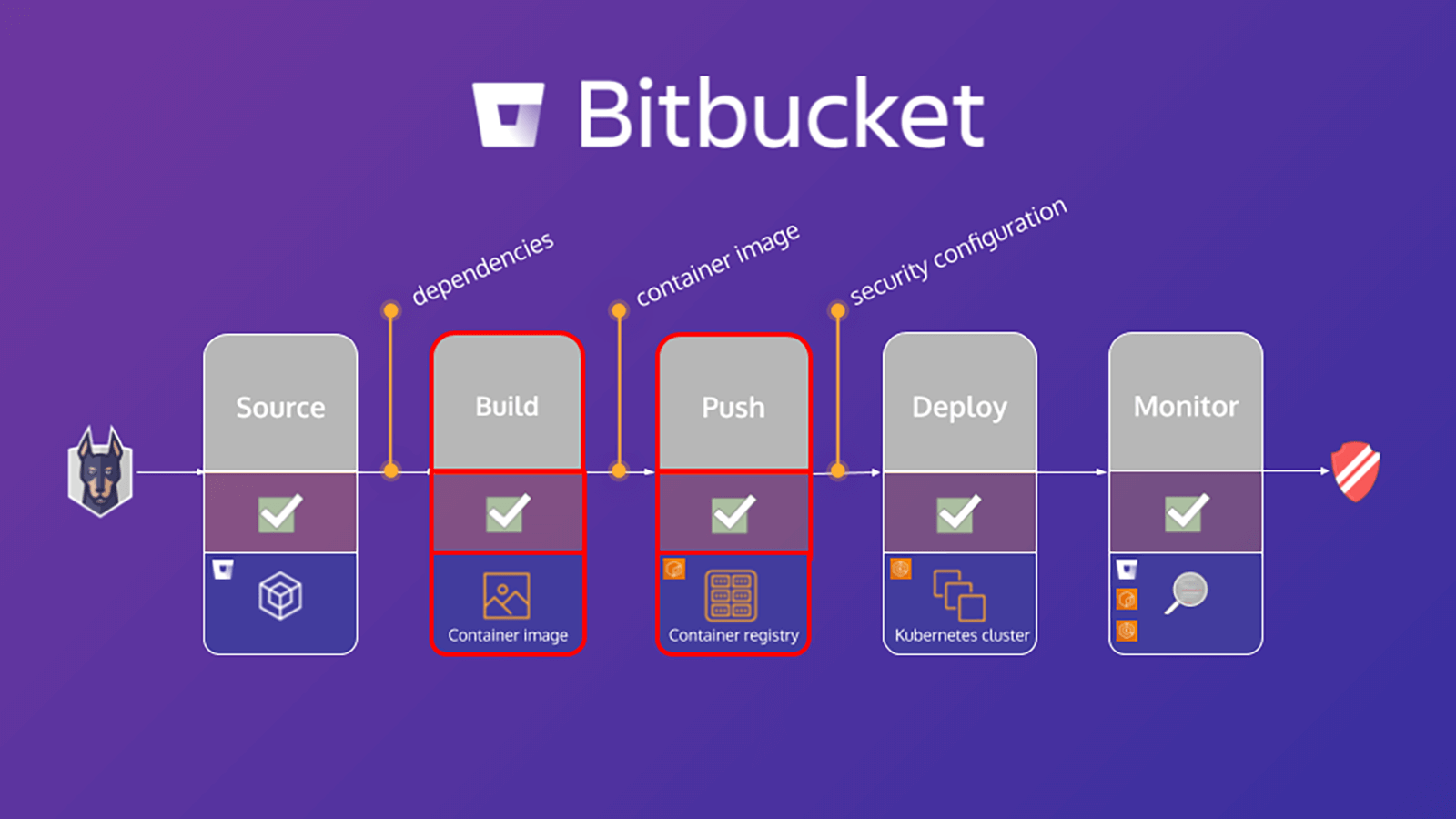
Este tutorial descreve como proteger o fluxo de trabalho de build no Bitbucket Pipelines com o Snyk. Uma etapa importante para proteger o ambiente é verificar e analisar o aplicativo e o projeto de contêiner baseado em Linux em busca de vulnerabilidades conhecidas, o que ajuda a identificar e reduzir vulnerabilidades de segurança. Os exercícios neste tutorial vão ajudar a proteger o aplicativo e contêiner, aproveitando o Snyk Pipe for Bitbucket Pipelines para verificar o arquivo de manifesto do aplicativo e a imagem base do contêiner para as dependências.
O tutorial, Como o Snyk e o Bitbucket Cloud tornam o DevSecOps viável, se concentra nas dependências dos aplicativos. No entanto, ao verificar também a imagem base do contêiner, você pode identificar:
- Os pacotes do sistema operacional (SO) instalados e gerenciados pelo gerenciador de pacotes
- Binários principais – camadas que não foram instaladas por meio do gerenciador de pacotes
Com base nesses resultados, o Snyk fornece conselhos e orientações, incluindo:
- As origens das vulnerabilidades nos pacotes do sistema operacional e dos binários principais
- Informações do upgrade da imagem base ou uma recomendação para recriar a imagem
- Camada Dockerfile em que o pacote afetado foi introduzido
- Versão fixa do sistema operacional e dos principais pacotes binários
Verificação de aplicativos no Bitbucket Pipeline
O arquivo bitbucket-pipelines.yml define a configuração de builds do Bitbucket Pipelines. Se você é novo no Bitbucket Pipelines, pode aprender mais sobre como começar aqui.
Este tutorial fornece um arquivo de exemplo bitbucket-pipelines.yml que contém etapas distintas mapeadas para o fluxo de trabalho. Começaremos com a verificação do aplicativo, criação da imagem do Docker e, em seguida, a verificação a imagem do contêiner. A seguir, uma análise mais minuciosa da etapa de verificação do aplicativo:
scan-app: &scan-app
- step:
name: "Scan open source dependencies"
caches:
- node
script:
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "npm"
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "package.json"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"Este exemplo aproveita o pipe do Snyk Scan no pipeline para realizar uma verificação do aplicativo. A fonte contém uma definição YAML completa de todas as variáveis compatíveis, mas apenas as incluídas nesse trecho são necessárias para esse propósito.
A seguir, há uma análise mais minuciosa de alguns deles:
1. SNYK_TOKEN é passado para o pipe como uma variável de repositório que foi definida antes no módulo [Configuração do Bitbucket]
2. PROJECT_FOLDER é a pasta onde o projeto está localizado e, em geral, é o local padrão. No entanto, neste exemplo, foi definida como app/goof e passada como um artefato para outras etapas do pipeline.
3. O padrão CODE_INSIGHTS_RESULTS é false (falso). No entanto, como queremos criar um relatório do Code Insight com os resultados do teste do Snyk, defina essa opção como true (verdadeiro).
4. SEVERITY_THRESHOLD relata itens iguais ou superiores ao nível oferecido. O padrão é low (baixo). Mas, neste caso, estamos interessados apenas em high (alto), então definimos essa variável de acordo.
5. O padrão DONT_BREAK_BUILD é false, o que é esperado. Em circunstâncias normais, você quer interromper a build se os itens forem encontrados. No entanto, para o propósito deste exercício de aprendizado, defina essa opção como true.
Você pode executar verificações de segurança do Snyk nas solicitações pull e visualizar os resultados no Code Insights com a ajuda do novo app Snyk Security Connect no Atlassian Marketplace. É fácil começar e você pode instalar o app com apenas alguns cliques.
Verifique as imagens do contêiner
Até 2022, mais de 75% das empresas globais vão executar aplicativos em contêineres em produção (Gartner). Junto com a adoção generalizada, houve um aumento nas vulnerabilidades de contêineres, com um crescimento quatro vezes maior nas vulnerabilidades relatadas pelo sistema operacional em 2018. E, no entanto, 80% dos desenvolvedores dizem que não testam as imagens de contêiner durante o desenvolvimento. Segundo eles, esse ponto não faz parte das responsabilidades deles ou estão acostumados a repassar esses itens a alguém no futuro, o que torna o dimensionamento da segurança de contêineres um desafio para empresas em rápido crescimento.
Verificação de imagens de contêiner no pipeline
Semelhante à seção anterior sobre Verificação de aplicativos, esta seção se concentra na configuração do arquivo bitbucket-pipelines.yml para criar a imagem do Docker para o aplicativo, verificar a imagem e enviá-la ao registro. Veja a seguir uma análise mais minuciosa da etapa de verificação da imagem do contêiner:
scan-push-image: &scan-push-image
- step:
name: "Scan and push container image"
services:
- docker
script:
- docker build -t $IMAGE ./app/goof/
- docker tag $IMAGE $IMAGE:${BITBUCKET_COMMIT}
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "docker"
IMAGE_NAME: $IMAGE
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "Dockerfile"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"O que cria a imagem do contêiner e a marca e, em seguida, aproveitando o pipe do Snyk Scan no pipeline para realizar uma verificação da imagem do contêiner. Mantenha os mesmos valores para CODE_INSIGHTS_RESULTS, SEVERITY_THRESHOLD e DONT_BREAK_BUILD. Também passa algumas variáveis adicionais compatíveis relevantes ao Snyk Pipe para entender a solicitação de uma verificação de imagem de contêiner em vez de uma verificação de aplicativo. Essa ação significa definir a configuração LANGUAGE para docker, declarar o IMAGE_NAME e passar a variável de repositório adequado, bem como definir o TARGET_FILE para Dockerfile.
O pipeline agora verifica a imagem do contêiner em busca de vulnerabilidades conhecidas, bem como o código do aplicativo.
Veja mais integrações para o Atlassian Open DevOps
Compartilhe este artigo
Próximo tópico
Leitura recomendada
Marque esses recursos para aprender sobre os tipos de equipes de DevOps ou para obter atualizações contínuas sobre DevOps na Atlassian.

Comunidade de DevOps
Caminho de aprendizagem de DevOps