Snyk Bitbucket Pipelines 集成以实现 DevSecOps

Simon Maple
Snyk 的现场首席技术官
通过将 Snyk 与 Bitbucket Pipelines 和 Jira 集成来实现 DevSecOps。
时间
5 分钟阅读。
观众
开发人员、安全/应用团队以及 DevOps/DevSecOps 工程师。
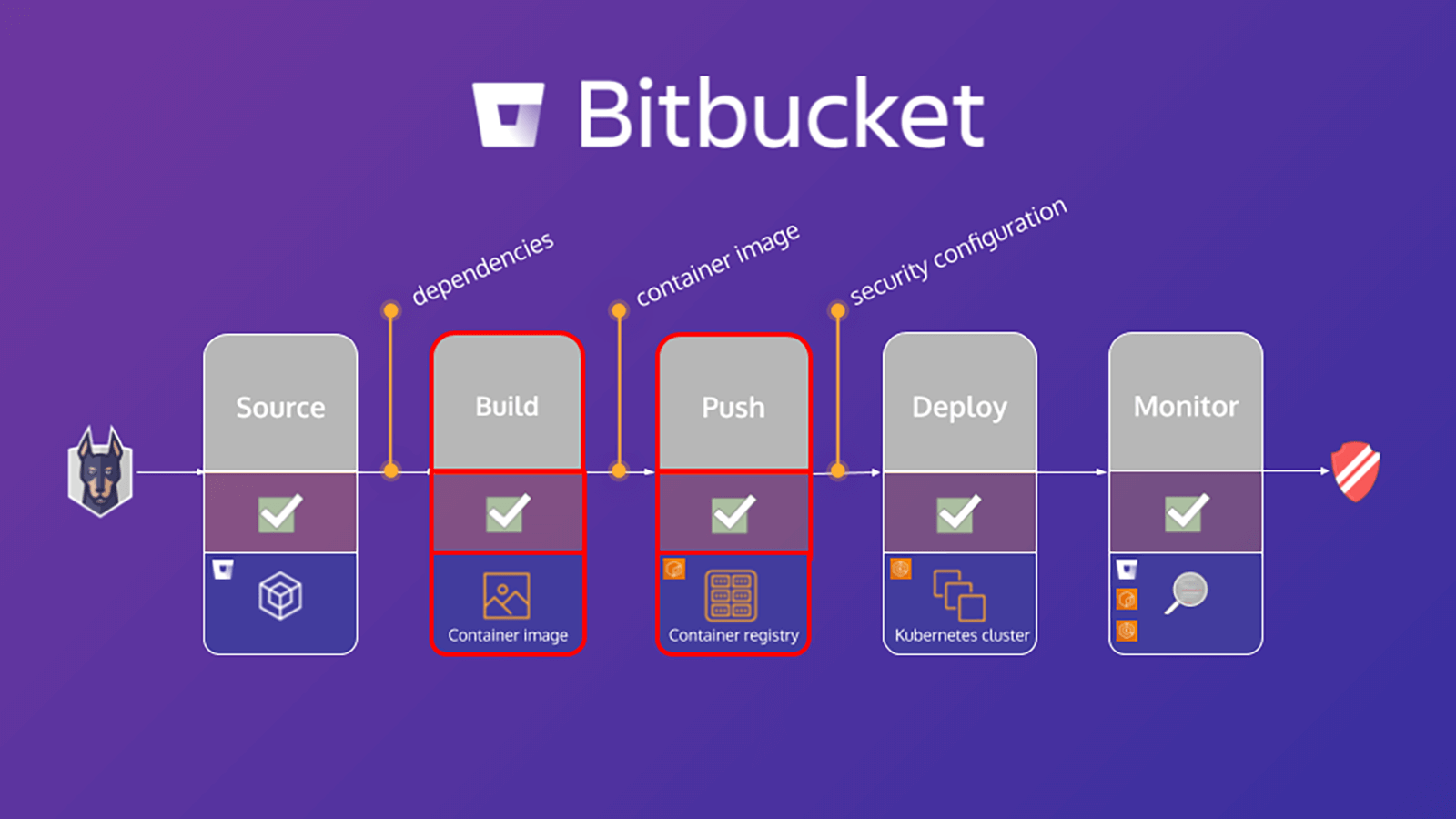
本教程概述如何使用 Snyk 在 Bitbucket Pipelines 上保护构建工作流。保护环境的一个重要步骤是扫描和分析应用以及基于 Linux 的容器项目中是否存在已知漏洞,这有助于您识别和抑制安全漏洞。本教程中的练习将利用适用于 Bitbucket Pipelines 的 Snyk Pipe 扫描应用清单文件和容器基础映像以查找其依赖关系,从而协助保护应用和容器的安全。
Snyk 和 Bitbucket Cloud 如何启用 DevSecOps 教程将重点介绍应用依赖关系。但是,通过同时扫描容器基础镜像,您可以检测到:
- 软件包管理器安装和管理的操作系统 (OS) 软件包
- 关键二进制文件 — 不是通过软件包管理器安装的层
根据这些结果,Snyk 将提供建议和指导,其中包括:
- OS 软件包和关键二进制文件中漏洞的起源
- 基础镜像升级详细信息或重新构建镜像的建议
- 引入受影响软件包的 Dockerfile 层
- 固定版本的操作系统和关键的二进制软件包
Bitbucket 管道中的应用扫描
bitbucket-pipelines.yml 文件定义了您的 Bitbucket Pipelines 构建配置。如果您不熟悉 Bitbucket Pipelines,可以在此处详细了解如何开始使用。
本教程提供了一个示例 bitbucket-pipelines.yml 文件,其中包含映射到工作流的不同步骤。我们将首先扫描应用,构建 Docker 镜像,然后扫描容器镜像。应用扫描步骤的详细说明如下:
scan-app: &scan-app
- step:
name: "Scan open source dependencies"
caches:
- node
script:
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "npm"
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "package.json"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"此示例利用管道中的 Snyk Scan 管道对应用执行扫描。源代码包含所有受支持变量的完整 YAML 定义,但只有此代码段中包含的变量才是必需的。
下面,深入了解其中的部分变量:
1. SNYK_TOKEN 将作为先前在 [Bitbucket 配置] 模块中定义的存储库变量而传递到管道中。
2. PROJECT_FOLDER 通常默认为项目所在的文件夹。但在本例中,我们将其设置为 app/goof,然后将其作为工件传递给管道中的其他步骤。
3. CODE_INSIGHTS_RESULTS 默认为 false。但是,由于我们要创建包含 Snyk 测试结果的 Code Insight 报告,请将其设为 true。
4. SEVERITY_THRESHOLD 将针对等于或高于所提供级别的事务进行报告。默认值为 low。但是在这种情况下,我们只对 high 感兴趣,所以我们相应地定义了这个变量。
5. DONT_BREAK_BUILD 的默认值为 false,此为预期设置。正常情况下,如果发现事务,您会想中断构建。但是,出于本学习练习的目的,请将其设为 true。
借助 Atlassian Marketplace 上新的 Snyk Security Connect 应用,您可以对拉取请求运行 Snyk 安全扫描,并在 Code Insights 中查看结果。入门非常简单,只需单击几下即可安装该应用。
扫描容器镜像
到 2022 年,超过 75% 的全球组织将在生产环境中运行容器化应用 (Gartner)。除被广泛采用外,容器漏洞也会激增,2018 年报告的操作系统漏洞就增加了 4 倍。但是,80% 的开发人员表示,他们在开发过程中不会测试容器镜像。他们要么说这不是他们的责任,要么习惯于有人在后续发现问题,从而使得扩展容器安全性成为快速增长的企业所面临的一大挑战。
管道中的容器镜像扫描
与上一节有关“应用扫描”的内容类似,本节重点介绍如何配置 bitbucket-pipelines.yml 文件以构建应用的 Docker 镜像、扫描此镜像,然后将该镜像推送到注册表。容器镜像扫描步骤的详细说明如下:
scan-push-image: &scan-push-image
- step:
name: "Scan and push container image"
services:
- docker
script:
- docker build -t $IMAGE ./app/goof/
- docker tag $IMAGE $IMAGE:${BITBUCKET_COMMIT}
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "docker"
IMAGE_NAME: $IMAGE
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "Dockerfile"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"分享这篇文章
下一个主题
推荐阅读
将这些资源加入书签,以了解 DevOps 团队的类型,或获取 Atlassian 关于 DevOps 的持续更新。

DevOps 社区
DevOps 学习路径