Integración de Snyk y Bitbucket Pipelines para adoptar DevSecOps

Simon Maple
Responsable de departamento tecnológico de campo de Snyk
Adopta un enfoque de DevSecOps integrando Snyk en Bitbucket Pipelines y Jira.
Duración
Lectura de 5 minutos.
Público
Desarrolladores, equipos de seguridad y aplicaciones e ingenieros de DevOps y DevSecOps.
Requisitos previos
Tienes una cuenta de Snyk. Empieza aquí.
Tienes una cuenta de Atlassian Bitbucket. Inicia sesión aquí o comienza aquí.
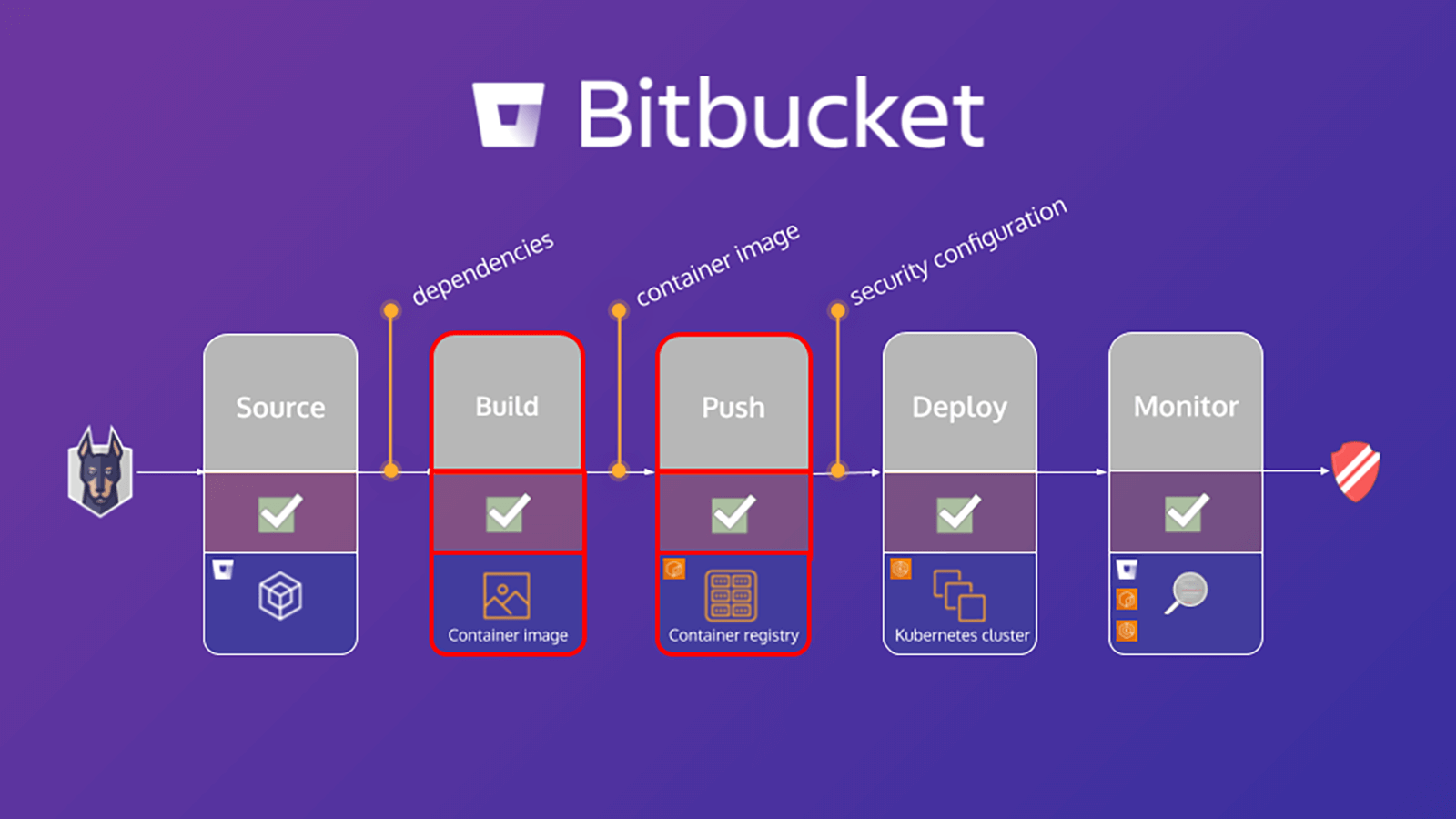
En este tutorial, se explica cómo proteger un flujo de trabajo de compilación en Bitbucket Pipelines con Snyk. Un paso importante que debes seguir a la hora de proteger tu entorno es el de analizar tanto tu aplicación como tu proyecto de contenedor basado en Linux en busca de vulnerabilidades conocidas, ya que ello te ayudará a identificar y mitigar las vulnerabilidades de seguridad. Los ejercicios de este tutorial te ayudarán a proteger tu aplicación y tu contenedor analizando el archivo de manifiesto de la aplicación y la imagen base del contenedor con Snyk Pipe for Bitbucket Pipelines a fin de detectar sus dependencias.
El tutorial, Desarrollo de un enfoque de DevSecOps con Snyk y Bitbucket Cloud, se centra en las dependencias de las aplicaciones. Sin embargo, si se analiza también la imagen base del contenedor, se puede detectar lo siguiente:
- Los paquetes del sistema operativo (SO) que ha instalado y que gestiona el administrador de paquetes
- Datos binarios de clave: capas que no se han instalado a través del administrador de paquetes
En función de estos resultados, Snyk ofrece asesoramiento y orientación en aspectos como los siguientes:
- Origen de las vulnerabilidades de los paquetes del sistema operativo y los datos binarios de clave
- Detalles de actualización de la imagen base o una recomendación para reconstruir la imagen
- Capa de Dockerfile en la que se ha introducido el paquete afectado
- Versión corregida de los paquetes del sistema operativo y de los binarios principales
Análisis de aplicaciones en tu canalización de Bitbucket Pipelines
El archivo bitbucket-pipelines.yml define la configuración de las compilaciones de Bitbucket Pipelines. Si es la primera vez que utilizas Bitbucket Pipelines, puedes obtener más información sobre su funcionamiento aquí.
Con este tutorial, se proporciona un archivo bitbucket-pipelines.yml de muestra que contiene distintos pasos asignados al flujo de trabajo. Comenzaremos analizando la aplicación, compilando la imagen de Docker y, después, realizando el análisis de la imagen del contenedor. A continuación, se muestra un análisis más detallado de los pasos que hay que seguir para analizar la aplicación:
scan-app: &scan-app
- step:
name: "Scan open source dependencies"
caches:
- node
script:
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "npm"
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "package.json"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"En este ejemplo, se hace uso del canal de Snyk Scan de la canalización para realizar un análisis de la aplicación. El código fuente contiene una definición completa en formato YAML de todas las variables compatibles, pero para este fin solo se requieren las incluidas en este fragmento de código.
Veamos más detenidamente algunas de ellas:
1. SNYK_TOKEN se transfiere al canal como variable de repositorio definida previamente en el módulo [Configuración de Bitbucket].
2. PROJECT_FOLDER es la carpeta en la que se encuentra el proyecto, y suele ser el valor predeterminado. Sin embargo, en este ejemplo, hemos establecido esta variable como app/goof y la hemos transferido como artefacto a otros pasos de su canalización.
3. El valor predeterminado de CODE_INSIGHTS_RESULTS es false, pero, como queremos crear un informe de Code Insight con los resultados de las pruebas de Snyk, hemos establecido este valor en true.
4. SEVERITY_THRESHOLD informa sobre incidencias con un nivel de gravedad igual o superior al establecido. Su valor predeterminado es low, pero, en este caso, solo nos interesan las de gravedad alta, por lo que hemos definido esta variable en high.
5. Como cabe esperar, el valor predeterminado DONT_BREAK_BUILD es false. En circunstancias normales, es conveniente interrumpir la compilación si se detectan incidencias, pero para este ejercicio define la variable en true.
Puedes ejecutar análisis de seguridad de Snyk en tus solicitudes de incorporación de cambios y ver los resultados en Code Insights con la ayuda de la nueva aplicación Snyk Security Connect de Atlassian Marketplace. Es muy fácil de usar y puedes instalarla con solo unos clics.
Análisis de imágenes de contenedores
Según Gartner, más del 75 % de las organizaciones internacionales ejecutará aplicaciones en contenedores en el entorno de producción para 2022. En paralelo a esta adopción generalizada, se ha producido un aumento de las vulnerabilidades de los contenedores, con un incremento que cuadruplica las vulnerabilidades de sistemas operativos notificadas en 2018. Sin embargo, el 80 % de los desarrolladores reconoce que no prueba las imágenes de sus contenedores durante la fase de desarrollo. Lo justifican afirmando que esto no entra dentro de sus competencias o que quienes intervienen en etapas posteriores suelen encargarse de las incidencias, de modo que escalar la seguridad de los contenedores supone un gran reto para las empresas de rápida expansión.
Análisis de imágenes de contenedores de tu canalización
Al igual que en la sección anterior sobre análisis de aplicaciones, esta sección se centra en configurar el archivo bitbucket-pipelines.yml para compilar la imagen de Docker de la aplicación, analizarla y, a continuación, enviarla al registro. A continuación, se muestra un análisis más detallado de los pasos que hay que seguir para analizar la imagen de un contenedor:
scan-push-image: &scan-push-image
- step:
name: "Scan and push container image"
services:
- docker
script:
- docker build -t $IMAGE ./app/goof/
- docker tag $IMAGE $IMAGE:${BITBUCKET_COMMIT}
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "docker"
IMAGE_NAME: $IMAGE
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "Dockerfile"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"Se trata de compilar la imagen del contenedor y etiquetarla para, a continuación, analizarla aprovechando el canal de Snyk Scan de la canalización. Para ello, define las variables CODE_INSIGHTS_RESULTS, SEVERITY_THRESHOLD y DONT_BREAK_BUILD con los mismos valores empleados en el ejercicio anterior. De este modo, también se transfieren algunas variables compatibles adicionales relevantes para Snyk Pipe con el fin de que se entienda la solicitud de un análisis de la imagen del contenedor, en lugar de un análisis de la aplicación. Esto consiste en establecer LANGUAGE como docker, declarar IMAGE_NAME y transferir la variable de repositorio adecuada, así como establecer TARGET_FILE como Dockerfile.
A continuación, tu canalización analiza la imagen del contenedor en busca de vulnerabilidades conocidas, así como el código de tu aplicación.
Compartir este artículo
Siguiente tema
Lecturas recomendadas
Consulta estos recursos para conocer los tipos de equipos de DevOps o para estar al tanto de las novedades sobre DevOps en Atlassian.

La comunidad de DevOps
Ruta de aprendizaje de DevOps