Articles
Tutoriels
Guides interactifs
Intégration de Snyk et Bitbucket Pipelines pour adopter l'approche DevSecOps

Simon Maple
Field CTO chez Snyk
Adoptez l'approche DevSecOps en intégrant Snyk à Bitbucket Pipelines et Jira.
Durée
5 minutes de lecture.
Public
Développeurs, équipes de sécurité/d'app et ingénieurs DevOps/DevSecOps.
Prérequis
Vous disposez d'un compte Snyk. Lancez-vous ici.
Vous disposez d'un compte Atlassian Bitbucket. Connectez-vous ici ou lancez-vous ici.
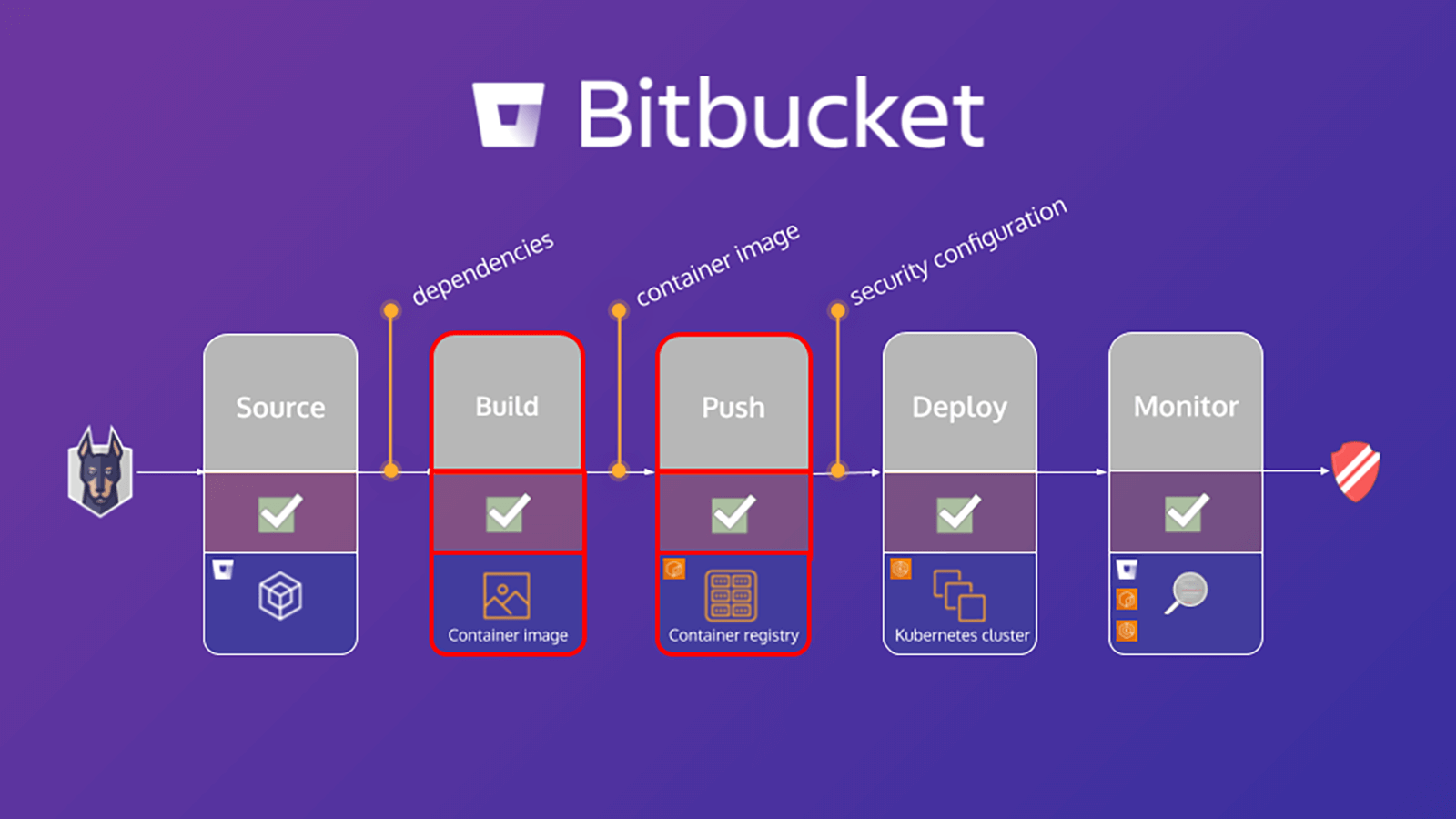
Ce tutoriel explique comment sécuriser votre workflow de développement sur Bitbucket Pipelines grâce à Snyk. Une étape importante de la sécurisation de votre environnement consiste à analyser votre app et votre projet de conteneur basé sur Linux pour détecter les vulnérabilités, ce qui vous permet d'identifier et de limiter les failles de sécurité. Les exercices de ce tutoriel vous aideront à sécuriser votre app et votre conteneur en utilisant Snyk Pipe for Bitbucket Pipelines pour analyser le fichier manifeste de l'app ainsi que l'image de base du conteneur à la recherche de ses dépendances.
Le tutoriel, Comment Snyk et Bitbucket Cloud favorisent une approche DevSecOps, est orienté sur les dépendances des apps. Toutefois, en analysant également l'image de base de votre conteneur, vous pouvez détecter ce qui suit :
- Les packages du système d'exploitation installés et gérés par le gestionnaire de packages
- Les binaires clés : couches qui n'ont pas été installées via le gestionnaire de packages
En fonction de ces résultats, Snyk fournit des conseils, notamment :
- L'origine des vulnérabilités dans les packages du système d'exploitation et les binaires clés
- Les informations sur la mise à niveau de l'image de base ou une recommandation de régénération de l'image
- Une couche Dockerfile sur laquelle le package affecté a été introduit
- Une version corrigée du système d'exploitation et des packages binaires clés
Analyser les apps dans votre pipeline Bitbucket
Le fichier bitbucket-pipelines.yml définit la configuration de vos builds Bitbucket Pipelines. Si vous débutez avec Bitbucket Pipelines, vous pouvez découvrir comment faire vos premiers pas ici.
Ce tutoriel fournit un exemple de fichier bitbucket-pipelines.yml qui contient des étapes distinctes mappées au workflow. Nous allons commencer par analyser l'app, puis nous créerons l'image Docker et analyserons l'image du conteneur. Voici un aperçu plus détaillé de l'étape d'analyse d'app :
scan-app: &scan-app
- step:
name: "Scan open source dependencies"
caches:
- node
script:
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "npm"
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "package.json"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"Cet exemple utilise le canal Snyk Scan dans le pipeline pour effectuer une analyse de l'app. La source contient une définition YAML complète de toutes les variables prises en charge, mais seules celles incluses dans ce snippet sont nécessaires à cette fin.
Voici un aperçu plus détaillé de certains de ces éléments :
1. SNYK_TOKEN est passé dans le pipe en tant que variable de dépôt précédemment définie dans le module [Configuration Bitbucket].
2. PROJECT_FOLDER est le dossier dans lequel le projet réside et est normalement défini par défaut. Cependant, dans cet exemple, nous définissons cette valeur sur app/goof, puis nous la transmettons en tant qu'artefact à d'autres étapes du pipeline.
3. La valeur par défaut de CODE_INSIGHTS_RESULTS est false (faux). Toutefois, comme nous voulons créer un rapport Code Insight avec les résultats des tests Snyk, définissez cette option sur true (vrai).
4. SEVERITY_THRESHOLD signale les problèmes dont le niveau est supérieur ou égal au niveau fourni. La valeur par défaut est low (faible). Mais dans ce cas, nous ne nous intéressons qu'à la valeur high (élevé). Nous avons donc défini cette variable en conséquence.
5. La valeur par défaut de DONT_BREAK_BUILD est false (faux), ce qui est attendu. Dans des circonstances normales, vous souhaitez interrompre le build en cas de détection de problèmes. Cependant, pour cet exercice d'apprentissage, définissez cette valeur sur true (vrai).
Vous pouvez exécuter des analyses de sécurité Snyk dans vos pull requests et afficher les résultats dans Code Insights à l'aide de la nouvelle app Snyk Security Connect de l'Atlassian Marketplace. Vous pouvez facilement vous lancer et installer l'app en quelques clics seulement.
Analyser les images de conteneur
D'ici 2022, plus de 75 % des entreprises mondiales exécuteront des apps conteneurisées en production (Gartner). Parallèlement à l'adoption généralisée, une augmentation des vulnérabilités de conteneurs a été constatée, avec une multiplication par 4 des vulnérabilités de système d'exploitation en 2018. Pourtant, 80 % des développeurs affirment ne pas tester leurs images de conteneur pendant le développement. Soit parce qu'ils affirment que cette tâche ne relève pas de leur responsabilité, soit parce qu'ils sont habitués à ce que quelqu'un détecte les problèmes plus tard dans le processus. En conséquence, la mise à l'échelle de la sécurité des conteneurs se révèle un défi pour les entreprises à croissance rapide.
Analyser des images de conteneurs dans votre pipeline
Tout comme la section précédente sur l'analyse des apps, cette section se concentre sur la configuration du fichier bitbucket-pipelines.yml afin de créer l'image Docker pour l'app, d'analyser l'image, puis de l'envoyer au registre. Voici un aperçu plus détaillé de l'étape d'analyse des images de conteneur :
scan-push-image: &scan-push-image
- step:
name: "Scan and push container image"
services:
- docker
script:
- docker build -t $IMAGE ./app/goof/
- docker tag $IMAGE $IMAGE:${BITBUCKET_COMMIT}
- pipe: snyk/snyk-scan:0.4.3
variables:
SNYK_TOKEN: $SNYK_TOKEN
LANGUAGE: "docker"
IMAGE_NAME: $IMAGE
PROJECT_FOLDER: "app/goof"
TARGET_FILE: "Dockerfile"
CODE_INSIGHTS_RESULTS: "true"
SEVERITY_THRESHOLD: "high"
DONT_BREAK_BUILD: "true"
MONITOR: "false"Il s'agit de créer l'image du conteneur et de la baliser, puis de tirer parti du pipe Snyk Scan dans le pipeline pour effectuer une analyse de l'image de conteneur. Conservez les mêmes valeurs pour CODE_INSIGHTS_RESULTS, SEVERITY_THRESHOLD et DONT_BREAK_BUILD. Cela transmet également quelques autres variables prises en charge. Celles-ci sont pertinentes pour le pipe Snyk afin de comprendre la demande d'analyse : une image de conteneur plutôt qu'une app. Il s'agit notamment de définir LANGUAGE sur docker, de déclarer la valeur IMAGE_NAME et de transmettre la variable de dépôt appropriée, ainsi que de définir la valeur de TARGET_FILE sur Dockerfile.
Votre pipeline analyse désormais l'image de conteneur à la recherche de vulnérabilités connues, ainsi que le code de votre app.
Découvrez plus d'intégrations pour Atlassian Open DevOps.
Partager cet article
Thème suivant
Lectures recommandées
Ajoutez ces ressources à vos favoris pour en savoir plus sur les types d'équipes DevOps, ou pour les mises à jour continues de DevOps chez Atlassian.

Communauté DevOps
Parcours de formation DevOps