記事
チュートリアル
インタラクティブ ガイド
AWS CloudWatch アラームを Bitbucket でデプロイする
.png?cdnVersion=3145)
Warren Marusiak
シニア テクニカル エバンジェリスト
当社のチームは Jira Software とさまざまな接続ツールを使用してアプリケーションを開発、デプロイ、管理する方法を説明するために、機械学習を使用してイメージにラベルを添付する AWS 上に構築されたシンプルなデモ アプリケーションである ImageLabeller を作成しました。
このページでは、Opsgenie で ImageLabeller を監視する方法について説明します。はじめに、ImageLabeller アーキテクチャのページをお読みの上、背景を確認することをお勧めします。
Opsgenie 統合用のアラーム リポジトリを追加する
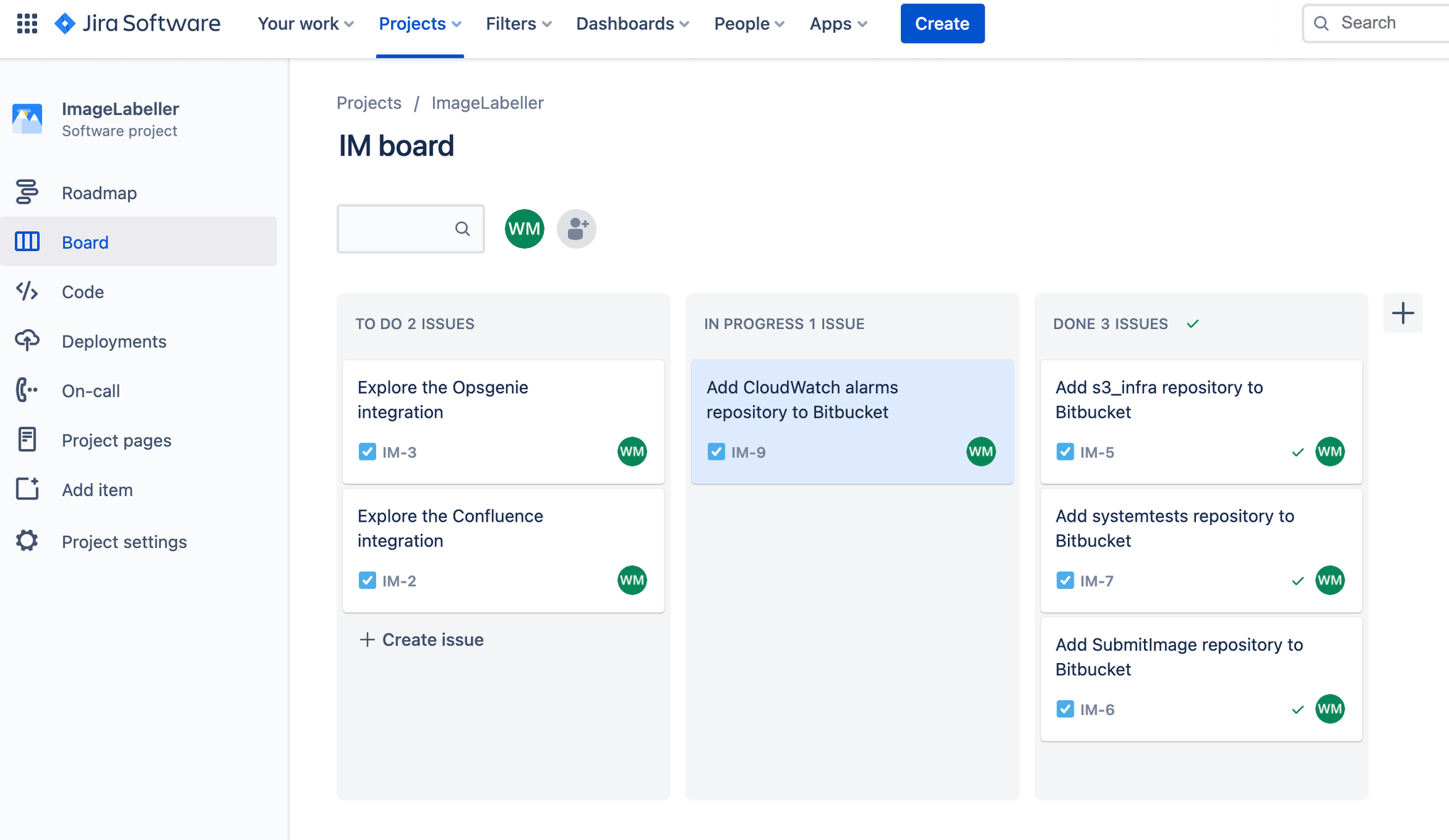
Jira に移動して、AWS CloudWatch アラーム リポジトリを Bitbucket に追加するための新しい Jira 課題を作成します。この例では、Jira 課題 ID は IM-9 です。
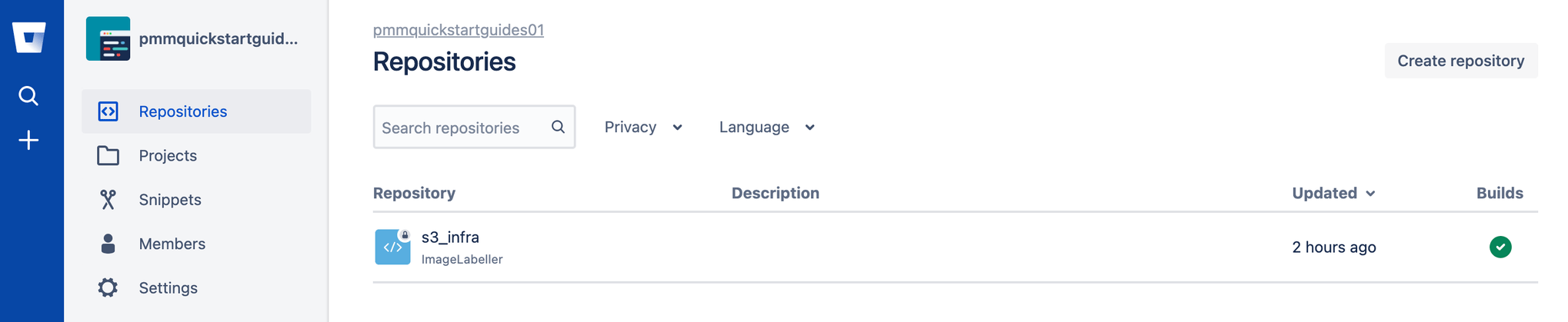
Bitbucket に移動して [作成]、[リポジトリ] の順にクリックします。
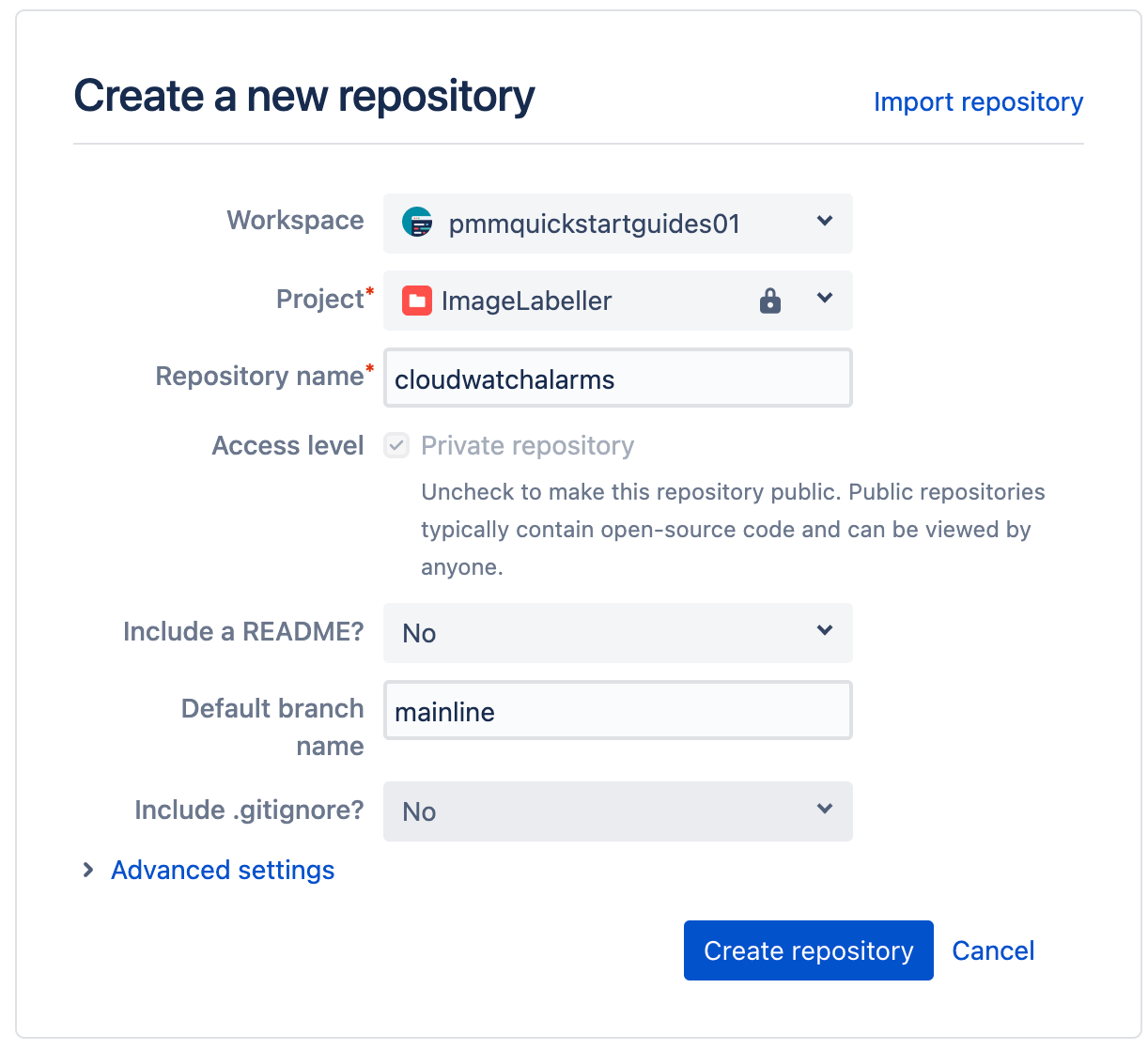
適切なワークスペースとプロジェクトを選択します。[デフォルトのブランチ名] を mainline に設定します。[リポジトリを作成] をクリックして続行します。
ターミナルの CloudWatchAlarms リポジトリに移動して以下を実行し、AWS CloudFormation テンプレート コードを Bitbucket にプッシュします。
git add --all
git commit -m "IM-9 add CloudWatchAlarms to Bitbucket"
git remote add origin git@bitbucket.org:pmmquickstartguides01/cloudwatchalarms.git
git branch -m mainline
git push -u origin mainlineAlarms template.yml
Description: 'A description'
Resources:
OpsGenieSNS:
Type: AWS::SNS::Topic
Properties:
DisplayName: 'Opsgenie'
Subscription:
- Endpoint: 'https://api.opsgenie.com/v1/json/cloudwatch?apiKey=a4449509-6998-4d55-841d-2e6b363520c7'
Protocol: 'HTTPS'
TopicName: 'Opsgenie'
SubmitImageLambdaAlarm:
Type: AWS::CloudWatch::Alarm
Properties:
AlarmActions:
- !Ref 'OpsGenieSNS'
AlarmDescription: 'SubmitImage Too Many Invocations'
ComparisonOperator: 'GreaterThanThreshold'
Dimensions:
- Name: FunctionName
Value: !ImportValue 'SubmitImageFunctionName'
EvaluationPeriods: 1
MetricName: 'Invocations'
Namespace: 'AWS/Lambda'
Period: 60
Statistic: 'Sum'
Threshold: 10SNS トピック サブスクリプション エンドポイントを、Opsgenie からコピーしたエンドポイント URL に設定します。SubmitImageLambdaAlarm は、SubmitImage AWS Lambda によって生成された単一のメトリックを監視します。呼び出しが 10 より多い場合は、1 分でアラームが鳴ります。
AWS にデプロイする bitbucket-pipelines.yml
ターミナルの CloudWatchAlarms リポジトリに移動して、Jira 課題 ID にちなんだ名前のブランチを作成します。
definitions:
steps:
- step: &deploy-test-usw1
name: Deploy Test us-west-1
script:
- pipe: atlassian/aws-cloudformation-deploy:0.10.0
variables:
AWS_ACCESS_KEY_ID: ${AWS_ACCESS_KEY_ID}
AWS_SECRET_ACCESS_KEY: ${AWS_SECRET_ACCESS_KEY}
AWS_DEFAULT_REGION: 'us-west-1'
STACK_NAME: 'OpenDevOpsAlarms'
CAPABILITIES: ['CAPABILITY_IAM', 'CAPABILITY_AUTO_EXPAND']
WAIT: 'true'
TEMPLATE: 'template.yml'
- step: &deploy-staging-use2
name: Deploy Staging us-east-2
script:
- pipe: atlassian/aws-cloudformation-deploy:0.10.0
variables:
AWS_ACCESS_KEY_ID: ${AWS_ACCESS_KEY_ID}
AWS_SECRET_ACCESS_KEY: ${AWS_SECRET_ACCESS_KEY}
AWS_DEFAULT_REGION: 'us-east-2'
STACK_NAME: 'OpenDevOpsAlarms'
CAPABILITIES: ['CAPABILITY_IAM', 'CAPABILITY_AUTO_EXPAND']
WAIT: 'true'
TEMPLATE: 'template.yml'
- step: &deploy-production-usw2
name: Deploy Production us-west-2
script:
- pipe: atlassian/aws-cloudformation-deploy:0.10.0
variables:
AWS_ACCESS_KEY_ID: ${AWS_ACCESS_KEY_ID}
AWS_SECRET_ACCESS_KEY: ${AWS_SECRET_ACCESS_KEY}
AWS_DEFAULT_REGION: 'us-west-2'
STACK_NAME: 'OpenDevOpsAlarms'
CAPABILITIES: ['CAPABILITY_IAM', 'CAPABILITY_AUTO_EXPAND']
WAIT: 'true'
TEMPLATE: 'template.yml'
- step: &deploy-production-use1
name: Deploy Proudction us-east-1
script:
- pipe: atlassian/aws-cloudformation-deploy:0.10.0
variables:
AWS_ACCESS_KEY_ID: ${AWS_ACCESS_KEY_ID}
AWS_SECRET_ACCESS_KEY: ${AWS_SECRET_ACCESS_KEY}
AWS_DEFAULT_REGION: 'us-east-1'
STACK_NAME: 'OpenDevOpsAlarms'
CAPABILITIES: ['CAPABILITY_IAM', 'CAPABILITY_AUTO_EXPAND']
WAIT: 'true'
TEMPLATE: 'template.yml'
- step: &deploy-production-cac1
name: Deploy Production ca-central-1
script:
- pipe: atlassian/aws-cloudformation-deploy:0.10.0
variables:
AWS_ACCESS_KEY_ID: ${AWS_ACCESS_KEY_ID}
AWS_SECRET_ACCESS_KEY: ${AWS_SECRET_ACCESS_KEY}
AWS_DEFAULT_REGION: 'ca-central-1'
STACK_NAME: 'OpenDevOpsAlarms'
CAPABILITIES: ['CAPABILITY_IAM', 'CAPABILITY_AUTO_EXPAND']
WAIT: 'true'
TEMPLATE: 'template.yml'
pipelines:
default:
- step:
<<: *deploy-test-usw1
deployment: Test us-west-1
- step:
<<: *deploy-staging-use2
deployment: Staging us-east-2
branches:
mainline:
- step:
<<: *deploy-production-usw2
deployment: Production us-west-2
- step:
<<: *deploy-production-use1
deployment: Production us-east-1
- step:
<<: *deploy-production-cac1
deployment: Production ca-central-1パイプラインを実行する前に、パイプラインを有効にしてデプロイ環境をセットアップし、AWS アクセス キーをリポジトリに追加する必要があることにご注意ください。
フィーチャー ブランチにプッシュ
コマンド ラインから次のコマンドを実行して、CloudWatchAlarms リポジトリの IM-9 ブランチに変更をプッシュします。Jira 課題 ID とブランチ名をコミット メッセージに含めて、プロジェクトで何が起こっているかを Jira Bitbucket 統合で追跡できるようにします。
git add --all
git commit -m "IM-9 add bitbucket-pipelines.yml to CloudWatchAlarms"
git push -u origin IM-9[Pipelines]、[IM-9] の順にクリックして、実行中のパイプラインを確認します。
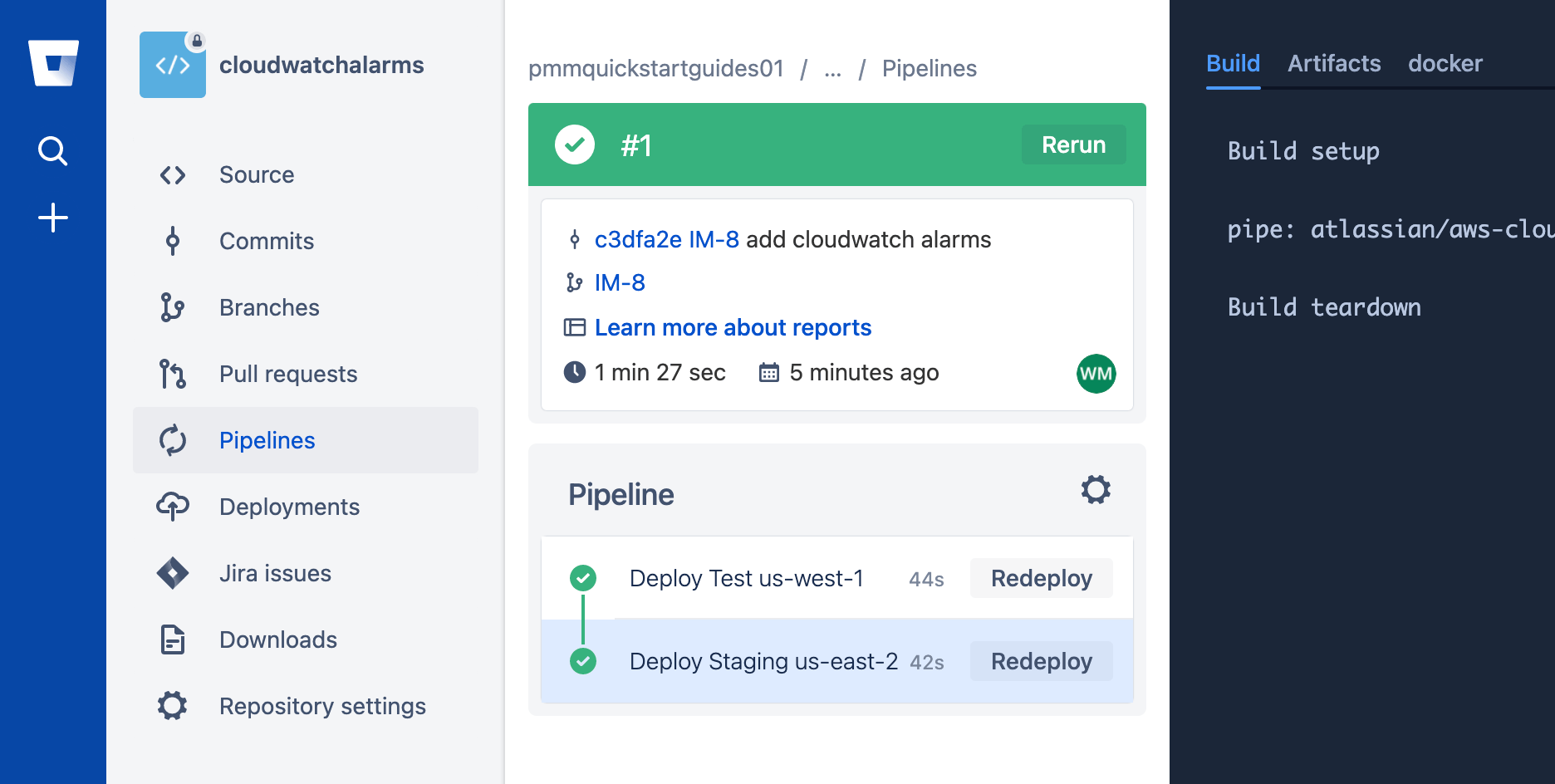
プルリクエストを作成する
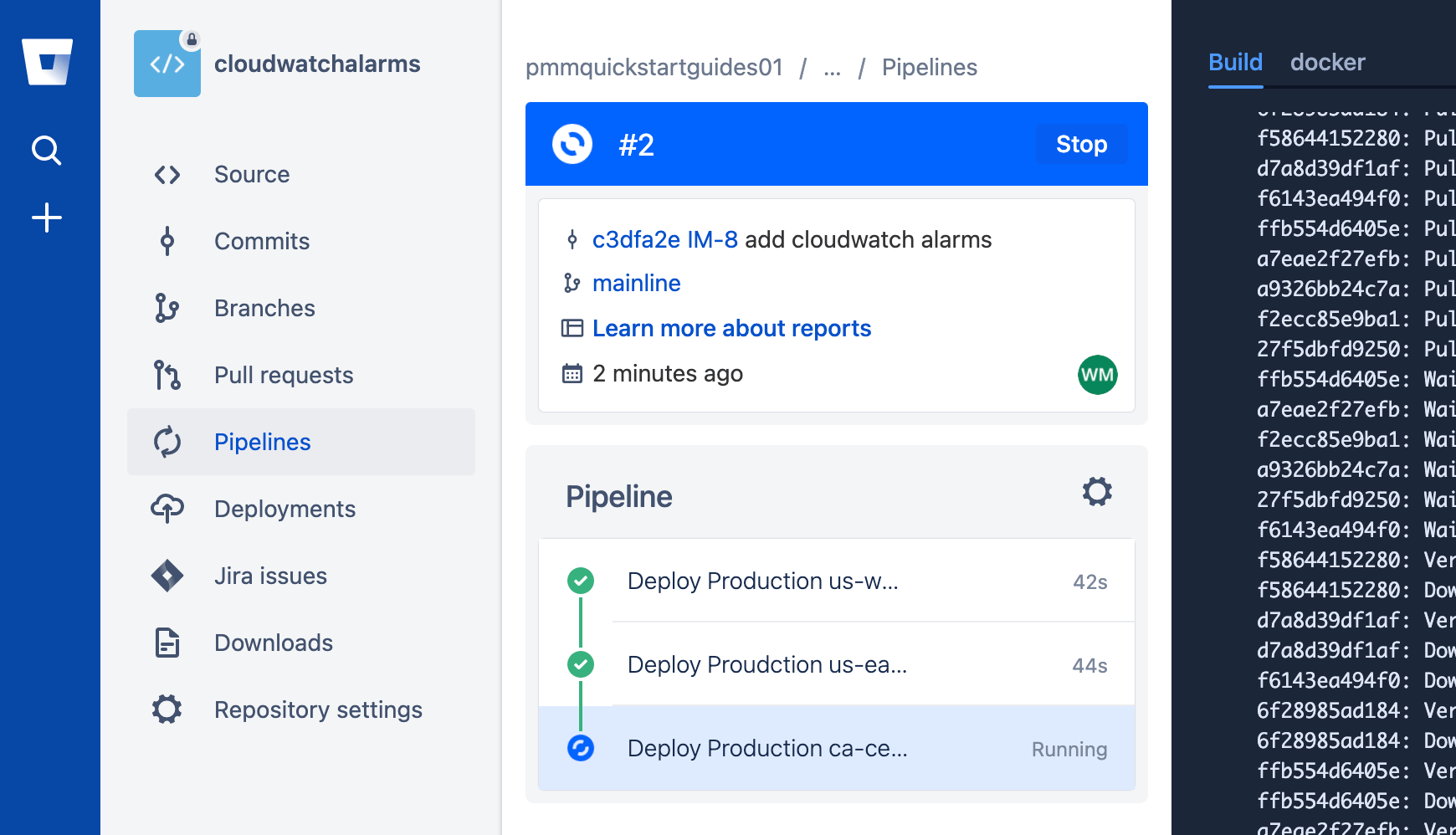
プル リクエストを作成するには [プル リクエスト]、[プル リクエストを作成] の順にクリックします。プル リクエストが終了したら [Pipelines] をクリックして本番環境のデプロイを確認します。
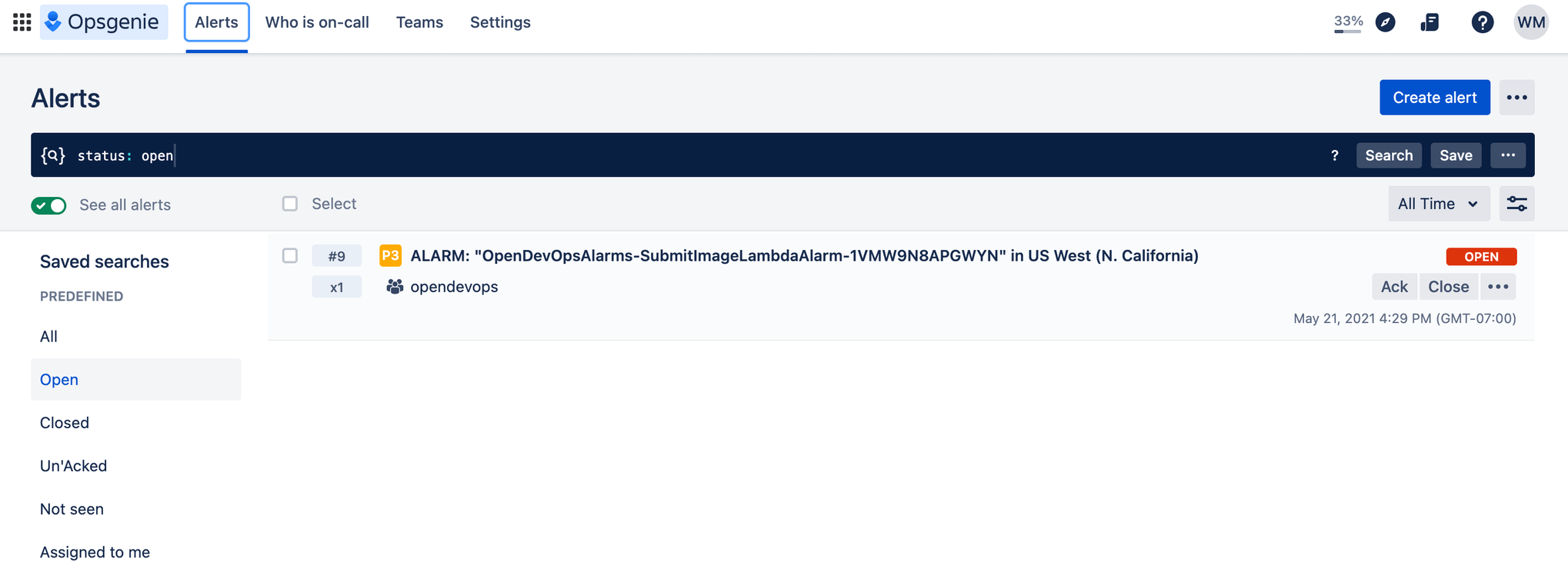
アラームのテスト
先ほど設定した AWS CloudWatch アラームをトリガーするか、[アラートを作成] をクリックしてアラートを生成します。
おめでとうございます、これで完了です。ImageLabeller が稼動しています。
この記事を共有する
次のトピック
おすすめコンテンツ
次のリソースをブックマークして、DevOps チームのタイプに関する詳細や、アトラシアンの DevOps についての継続的な更新をご覧ください。

DevOps コミュニティ
DevOps ラーニング パス