Praktyki dotyczące bezpieczeństwa
Wierzymy, że każdy zespół może dokonać niesamowitych rzeczy. Naszą misją jest uwolnienie tego potencjału w każdym zespole, niezależnie od jego rozmiaru czy branży, a co za tym idzie, przyczynienie się do postępu ludzkości dzięki korzystaniu z naszego oprogramowania.
Wiemy, że Twoja misja jest dla Ciebie równie ważna, jak nasza misja dla nas, a informacje stanowią podstawę działalności oraz życia każdego z nas. Dlatego w naszych działaniach zawsze skupiamy się na zaufaniu klientów, a bezpieczeństwo jest naszym najwyższym priorytetem. Prowadzimy nasz program zapewniania bezpieczeństwa w sposób przejrzysty, aby nasi klienci czuli się doinformowani i bezpieczni, korzystając z naszych produktów i usług.
Dowiedz się więcej na temat naszego podejścia do bezpieczeństwa oraz roli, jaką w jego zapewnianiu mogą odegrać sami klienci.
O ile nie wskazano inaczej, informacje zamieszczone na tej stronie dotyczą produktów Atlassian Cloud — Jira, Confluence i Bitbucket.
Nasze podejście do bezpieczeństwa
W tej części opiszemy podejście Atlassian do kwestii bezpieczeństwa. Przedstawiono w niej najważniejsze kroki, jakie podejmujemy, oraz środki kontroli wdrażane przez nas w wielu dziedzinach bezpieczeństwa w celu zabezpieczenia zarówno naszych własnych środowisk (w tym naszych platform chmurowych), jak i procesów, które stosujemy, aby dostarczać naszym klientom i użytkownikom możliwie jak najbezpieczniejsze produkty.
Nasza filozofia bezpieczeństwa
Nasze podejście do bezpieczeństwa opiera się na kilku podstawowych kwestiach:
- Chęć bycia dla innych firm liderem w dziedzinie bezpieczeństwa chmury i produktów.
- Spełnianie wszystkich wymagań klientów dotyczących bezpieczeństwa chmury i przekraczanie wymagań stawianych przez branżowe normy i certyfikaty w zakresie bezpieczeństwa.
- Otwartość i przejrzystość w sprawie naszych programów, procesów i wskaźników. To oznacza dzielenie się własnymi doświadczeniami i zachęcanie innych dostawców chmury do tego samego, a także wyznaczanie nowych standardów dla klientów.
W tej części przedstawiamy szereg działań i inicjatyw, które podjęliśmy, aby realizować tę filozofię w kontekście wspomnianych podstawowych kwestii.
Jesteśmy również dumni z faktu, że wiele spośród naszych flagowych produktów stanowi podstawę i krytyczny składnik naszych wewnętrznych procesów i przepływów pracy realizowanych na co dzień w Atlassian. Przykładowo nasze rozwiązania Jira i Confluence stanowią kluczowe filary, na których opiera się nasze podejście do programów zarządzania incydentami i lukami w zabezpieczeniach. To oznacza, że zainwestowaliśmy w zabezpieczenie naszych produktów nie tylko dlatego, że jedna z naszych kluczowych wartości to „nie wkurzamy naszych klientów”, ale także dlatego, że sami korzystamy z tych samych produktów.
Nasz zespół
Wiemy, że to samo powiedzieliby przedstawiciele większości firm, ale jesteśmy niezwykle dumni z naszego zespołu ds. bezpieczeństwa. Wierzymy, że udało nam się pozyskać najlepszych i najzdolniejszych specjalistów w branży oraz zapewnić im warunki do dalszego rozwoju. Nasz zespół ds. bezpieczeństwa liczy ponad 100 osób zatrudnionych w naszych biurach w Sydney, Amsterdamie, Bengaluru, Austin, Mountain View, San Francisco i Nowym Jorku, a także pracujących zdalnie. W związku z priorytetowym traktowaniem kwestii bezpieczeństwa przez firmę Atlassian zespół wciąż się rozrasta. W jego skład wchodzi wiele zespołów podrzędnych, takich jak:
- Zespół ds. bezpieczeństwa produktów — odpowiedzialny za bezpieczeństwo naszych produktów i platform.
- Zespół ds. bezpieczeństwa ekosystemu — odpowiedzialny za bezpieczeństwo naszego sklepu Marketplace oraz dodatków.
- Zespół ds. wykrywania i reagowania — odpowiedzialny za wykrywanie incydentów związanych z bezpieczeństwem i reagowanie na nie
- Red Team — odpowiedzialny za imitowanie wrogich ataków i prowadzenie działań w zakresie wykrywania i reagowania
- Zespół ds. architektury zabezpieczeń — odpowiedzialny za definiowanie wymagań dotyczących bezpieczeństwa naszych produktów i platform.
- Zespół ds. bezpieczeństwa korporacyjnego — odpowiedzialny za nasze bezpieczeństwo wewnętrzne związane z siecią i aplikacjami korporacyjnymi.
- Zespół ds. zaufania — odpowiedzialny za monitorowanie oczekiwań klientów i reagowanie na nie, a także za zapewnianie przejrzystości naszych procesów i praktyk.
- Zespół programistów i inżynierów ds. niezawodności lokalizacji — odpowiedzialny za tworzenie i obsługę narzędzi wykorzystywanych przez zespół ds. bezpieczeństwa.
- Zespół ds. podnoszenia świadomości i szkoleń — odpowiedzialny za zapewnienie naszym pracownikom i partnerom wiedzy potrzebnej do bezpiecznej pracy.
Chociaż nasz zespół ds. bezpieczeństwa wciąż się rozrasta, to w naszej misji, polegającej na osiągnięciu wyższego poziomu bezpieczeństwa, uczestniczą wszyscy pracownicy Atlassian, o czym stale im przypominamy. Chcemy być liderami w dziedzinie bezpieczeństwa w chmurze, spełniać wszystkie oczekiwania naszych klientów w tej kwestii, przekraczać wymagania wszystkich norm i certyfikatów branżowych, a także z dumą publikować szczegóły na temat tego, jak chronimy dane klientów. Dbamy o to, aby nasze cele i wizja były jasne dla każdej osoby zatrudnionej w Atlassian.
Dodatkowe programy używane do wspierania bezpieczeństwa
Skupiamy się na podstawowych kwestiach związanych z bezpieczeństwem, ale wdrożyliśmy także całą gamę programów, dzięki którym nasze podejście do bezpieczeństwa zachowuje szeroki zasięg i proaktywny charakter. Należą do nich:
Program wykrywania naruszeń bezpieczeństwa
Program wykrywania naruszeń bezpieczeństwa stanowi uzupełnienie naszych procesów reagowania na incydenty. Częścią naszego standardowego procesu zarządzania incydentami jest osobny program proaktywnego tworzenia wyszukiwań i alertów dotyczących nie tylko tych rodzajów incydentów, z którymi mamy do czynienia dzisiaj, ale także tych, z którymi będziemy się mierzyć w przyszłości.
Program wykrywania błędów
W ramach naszego programu wykrywania błędów, konsekwentnie uznawanego za jeden z najlepszych w branży, zaufana społeczność dziesiątek tysięcy badaczy stale testuje nasze produkty i zgłasza nam wszelkie znalezione luki w zabezpieczeniach.
Ciągłe doskonalenie naszego programu zapewniania bezpieczeństwa
Zależy nam na tym, aby nasz program zapewniania bezpieczeństwa wciąż należał do ścisłej czołówki i stanowił punkt odniesienia dla innych firm z branży. Wiemy, że wymaga to ciągłej weryfikacji naszego podejścia do bezpieczeństwa (również w porównaniu z konkurencją) oraz identyfikowania możliwości poprawy.
W tym celu poddaliśmy się (i będziemy nadal się poddawać) licznym ocenom dojrzałości naszego programu zapewniania bezpieczeństwa przez niezależne firmy zajmujące się doradztwem w tym zakresie. Otrzymane wyniki, w tym kluczowe zalecenia, wykorzystujemy w celu wyeliminowania wszelkich braków i wprowadzenia ulepszeń.
W celu ukierunkowania naszego wewnętrznego doskonalenia wdrożyliśmy również szereg programów dotyczących różnych aspektów bezpieczeństwa, takich jak bezpieczeństwo produktów czy wykrywanie i reagowanie. Na potrzeby każdego z tych programów zdefiniowaliśmy wskaźniki, których oceny dokonuje zespół ds. zarządzania bezpieczeństwem. Dzięki tym wskaźnikom możemy określać obszary wymagające poprawy oraz podejmować odpowiednie działania w ramach każdej z naszych głównych kompetencji.
Więcej informacji
Zabezpieczenie naszego środowiska wewnętrznego
Skuteczne podejście do bezpieczeństwa rozpoczyna się od uporządkowania własnego podwórka, a w szczególności zabezpieczenia naszych własnych środowisk wewnętrznych. Podejmujemy szereg kroków, aby to osiągnąć.
Włączanie zabezpieczeń do naszej architektury sieciowej
Atlassian praktykuje wielopoziomowe podejście do zabezpieczenia własnych sieci. Wdrażamy środki kontroli w każdej warstwie naszych środowisk chmurowych, dzieląc posiadaną infrastrukturę według stref, środowisk i usług. Wdrożyliśmy ograniczenia strefowe, które obejmują restrykcje dotyczące ruchu sieciowego związanego z biurami/pracownikami, danymi klientów, procesami CI/CD oraz strefami zdemilitaryzowanymi (DMZ). Stosujemy również separację środowisk, aby ograniczyć łączność między środowiskami produkcyjnymi i nieprodukcyjnymi, a dane produkcyjne nie są replikowane poza środowiska produkcyjne.
Usługi muszą mieć wyraźne upoważnienie do komunikacji z innymi usługami zdefiniowane na liście dozwolonych do uwierzytelniania. Kontrolujemy dostęp do naszych sieci wrażliwych poprzez użycie routingu w obrębie wirtualnej chmury prywatnej (VPC), reguł zapory oraz sieci zdefiniowanych programowo, a wszystkie połączenia z tymi sieciami są szyfrowane. Wdrożyliśmy również system wykrywania nieautoryzowanego dostępu, zarówno w naszych sieciach biurowych, jak i produkcyjnych, aby wykrywać potencjalne naruszenia zabezpieczeń.
Zabezpieczanie dostępu do naszych sieci w myśl zasady Zero Trust
Atlassian zabezpiecza dostęp do swojej sieci korporacyjnej, swoich aplikacji i środowisk chmurowych zgodnie z modelem Zero Trust.
Podejście do bezpieczeństwa Zero Trust wykracza poza tradycyjne metody zabezpieczenia sieci, które polegają przede wszystkim na uwierzytelnianiu użytkowników w celu określenia uprawnień dostępu do zasobów sieciowych. Takie metody mogą stanowić zagrożenie, ponieważ potencjalnie umożliwiają niezaufanym i niebezpiecznym urządzeniom naruszenie bezpieczeństwa. W związku z tym wiele organizacji, w tym Atlassian, przyjęło model, w którym dostęp do sieci mogą uzyskać tylko zaufane urządzenia spełniające określone wymagania bezpieczeństwa.
Atlassian zarządza dostępem do środowisk produkcyjnych i usługowych, integrując tożsamość użytkowników i punktów końcowych z kompleksowym zestawem sygnałów pochodzących z urządzeń. Te sygnały są stale odbierane z naszego oprogramowania do zarządzania urządzeniami mobilnymi (MDM), rozwiązania do wykrywania i reagowania w punktach końcowych (EDR) i rejestru zasobów.
Zarządzanie bezpiecznym dostępem do naszych systemów i usług
Firma Atlassian stosuje dobrze zdefiniowany proces aprowizacji (przypisywania i unieważniania) dostępu użytkowników w przypadku wszystkich systemów i usług. Ustanowiliśmy przepływ pracy łączący nasz system zarządzania HR z systemem aprowizacji dostępu. Stosujemy mechanizm kontroli dostępu oparty na rolach, wykorzystujący wstępnie zdefiniowane profile użytkowników, który pozwala ograniczyć dostęp użytkowników wyłącznie do zakresu zgodnego z zajmowanymi przez nich stanowiskami. Wszystkie konta użytkowników muszą zostać zatwierdzone przez kierownictwo, zanim otrzymają oni dostęp do danych, aplikacji, infrastruktury lub składników sieci.
Wykorzystując naszą architekturę Zero Trust, kontrolujemy dostęp do naszych aplikacji korporacyjnych dzięki platformie logowania jednokrotnego. Aby uzyskać dostęp do dowolnej z naszych aplikacji, pracownik musi uwierzytelnić się za pośrednictwem tej platformy, łącznie z użyciem drugiego składnika uwierzytelniania. W zależności od aplikacji pracownicy muszą uwierzytelniać się za pomocą kluczy FIDO2 lub za pośrednictwem aplikacji mobilnej do uwierzytelniania udostępnionej pracownikom firmy Atlassian — mniej bezpieczne metody uwierzytelniania, takie jak wiadomości SMS i hasła jednorazowe wysyłane na telefon, nie są obsługiwane. Firma Atlassian przyjęła takie podejście, aby mieć pewność, że zastosowany proces uwierzytelniania jest wysoce odporny na ataki phishingowe oraz ataki typu man-in-the-middle. Jeśli osoba przeprowadzająca atak posiada odpowiednie umiejętności, może dojść do naruszenia zabezpieczeń każdego systemu obejmującego wysyłanie kodów w wiadomości tekstowej.
Zabezpieczanie naszych urządzeń końcowych
Laptopy firmowe
Urządzenia wchodzące w skład parku korporacyjnego firmy Atlassian są skonfigurowane tak, aby chronić nasze dane i zmniejszać ryzyko naruszenia bezpieczeństwa urządzeń końcowych. W ramach naszego programu Zero Trust urządzenia, które odbiegają od zatwierdzonego standardu, mają automatycznie blokowany dostęp do systemów firmy Atlassian.
Mechanizmy kontrolne wdrożone na urządzeniach firmy Atlassian obejmują następujące pozycje:
- Centralne zarządzanie urządzeniami — nasze rozwiązanie do zarządzania urządzeniami mobilnymi (MDM) odpowiada za wymuszanie konfiguracji zabezpieczeń (w tym testów porównawczych CIS) oraz wdrażanie oprogramowania/aktualizacji na wszystkich urządzeniach należących do firmy Atlassian.
- Kontrola aplikacji — kontrola aplikacji zapobiega uruchamianiu określonych typów legalnego oprogramowania (takich jak rozwiązania do zdalnego dostępu), które mogłyby zagrozić bezpieczeństwu naszych urządzeń.
- Zapory sieciowe na urządzeniach końcowych — zapobiegają narażeniu usług lokalnych na zagrożenia ze strony sieci.
- Antywirus / wykrywanie i reagowanie na urządzeniach końcowych (EDR) — wykrywa i blokuje złośliwe oprogramowanie, gromadzi dane dziennika i umożliwia naszemu centrum ds. operacji z zakresu bezpieczeństwa szybkie reagowanie na incydenty związane z bezpieczeństwem.
- Bezpieczne środowisko przeglądania — wszystkie przeglądarki używane przez personel są skonfigurowane tak, aby uniemożliwiały instalację i używanie złośliwych rozszerzeń oraz blokowały znane witryny wykorzystywane do phishingu lub witryny dystrybuujące złośliwe oprogramowanie.
- Szyfrowanie dysków / blokady ekranu — wszystkie urządzenia są w pełni szyfrowane i blokowane po okresie bezczynności.
Urządzenia mobilne/BYOD
Atlassian prowadzi program BYOD (urządzenia własne użytkowników) dla pracowników, którzy chcą korzystać ze swoich osobistych urządzeń mobilnych z systemem iOS lub Android w celu uzyskania dostępu do systemów korporacyjnych. Wszystkie urządzenia mobilne muszą:
- być zarejestrowane w naszym rozwiązaniu do zarządzania urządzeniami mobilnymi (MDM);
- mieć włączone pełne szyfrowanie dysków / blokady ekranu;
- mieć zainstalowany najnowszy system operacyjny Android/iOS.
Urządzenia mobilne działające w ramach programu BYOD mają ograniczony dostęp do systemów firmy Atlassian i nie mają dostępu do danych klientów.
Bezpieczeństwo w naszych codziennych działaniach
Dokładamy wszelkich starań, aby uwzględniać zabezpieczenia w każdym aspekcie naszych codziennych procesów roboczych. Chcemy, aby bezpieczeństwo stało się nieodłącznym elementem naszego sposobu pracy, co pozwoliłoby ograniczyć do minimum konieczność „modernizacji” i „dopasowywania” zabezpieczeń po fakcie.
Monitorowanie naszych zasobów informatycznych
Nasze systemy produkcyjne są umieszczone w infrastrukturze udostępnianej przez dostawców usług w chmurze. Ze względu na charakter usługi systemy te nie są monitorowane na poziomie sprzętowym. Stanowiące ich podstawę mikrousługi, w oparciu o które działają nasze produkty, są monitorowane w niestandardowej bazie danych „Usługa”. Ta baza danych jest aktualizowana automatycznie po wdrożeniu usługi.
Nasz zespół ds. technologii w miejscu pracy prowadzi wykaz zasobów wszystkich punktów końcowych, wykorzystując do śledzenia nasze własne oprogramowanie Jira.
Zarządzanie zmianami w naszym środowisku
Nasz proces zarządzania zmianami różni się nieco od tradycyjnego. Tradycyjne procesy zarządzania zmianami opierają się na hierarchii kontroli zmian przypominającej piramidę. Oznacza to, że gdy ktoś chce wprowadzić zmianę, musi przedstawić ją radzie, która ostatecznie ją zatwierdzi lub odrzuci.
Wdrożyliśmy podejście w stylu open source, które nazywamy „Peer Review, Green Build” (PRGB), czyli recenzja przez współpracownika i kompilacja gotowa do wdrożenia. W przeciwieństwie do tradycyjnego procesu zarządzania zmianami, podejście PRGB zakłada, że każda zmiana — czy to zmiana kodu, czy infrastruktury — jest sprawdzana przez co najmniej jednego współpracownika w celu wykrycia wszelkich problemów, jakie mogłaby potencjalnie spowodować. W zależności od stopnia krytyczności zmiany lub systemów, na które ma ona wpływ, zwiększamy liczbę recenzentów. Ufamy, że nasi inżynierowie wykryją problemy, a następnie zgłoszą je, zanim zmiana zostanie wdrożona. Taki proces dobrze się sprawdza, umożliwiając dynamiczne i adaptacyjne zarządzanie zmianami w naszym środowisku. Część „Green Build” naszego podejścia odnosi się do pomyślnej lub czystej kompilacji w naszym procesie CI/CD z uwzględnieniem nowo wprowadzonych zmian. Jeśli zmiana wprowadza składniki, które nie przejdą pomyślnie dowolnego testu integracji, działania, jednostkowego lub zabezpieczeń, kompilacja zostanie odrzucona i powróci do pierwotnego wniosku o zmianę, aby umożliwić rozwiązanie wszelkich problemów.
Zarządzanie konfiguracjami w naszych systemach
Liczba inżynierów i architektów, którzy mogą instalować oprogramowanie w naszym środowisku produkcyjnym, jest ograniczona. W większości przypadków instalacja oprogramowania jest niemożliwa. W naszych środowiskach produkcyjnych do zarządzania konfiguracjami i zmianami na serwerach wykorzystujemy narzędzia do zarządzania konfiguracjami. Zmiany wprowadzane bezpośrednio w tych systemach są ustawione tak, aby mogły być zastępowane przez zatwierdzoną konfigurację wypchniętą za pośrednictwem tych narzędzi do zarządzania konfiguracjami, co pozwala zapewnić spójność. Bazujemy na standardowych obrazach maszyn Amazon (Amazon Machine Image, AMI). Wszystkie zmiany w naszych obrazach AMI lub systemach operacyjnych muszą być dokonywane z wykorzystaniem naszego standardowego procesu zarządzania zmianami. Śledzimy i zgłaszamy konfiguracje wyjątków oraz wdrożyliśmy mechanizm izolacji zasobów, aby problemy z usługami nie wpływały na inne usługi. Wykorzystujemy również nasz proces PRGB, w ramach którego wielu recenzentów zatwierdza zmiany w konfiguracji wypychane za pośrednictwem narzędzi do zarządzania konfiguracjami. Wszystkie kompilacje są podpisane kryptograficznie i jedynie podpisane kompilacje mogą być uruchomione w naszym środowisku produkcyjnym.
Korzystanie z dzienników
Korzystamy z platformy do zarządzania informacjami i zdarzeniami zabezpieczeń (SIEM) w celu agregowania dzienników z różnych źródeł, stosowania reguł monitorowania do tych zagregowanych dzienników oraz oznaczania wszelkich podejrzanych aktywności. Nasze procesy wewnętrzne określają sposób klasyfikowania, dalszego badania i odpowiedniego eskalowania tych alertów. Dzienniki kluczowych systemów są przekazywane dalej z każdego systemu, w którym dzienniki są tylko do odczytu. Zespół ds. bezpieczeństwa Atlassian tworzy alerty na naszej platformie analizy zabezpieczeń i monitoruje wskaźniki pod kątem naruszeń. Nasze zespoły inżynierów ds. niezawodności lokalizacji (SRE) wykorzystują tę platformę do monitorowania problemów z dostępnością lub wydajnością. Dzienniki są przechowywane przez 30 dni w dynamicznej kopii zapasowej i przez 365 dni w kopii zapasowej offline.
Dzienniki kluczowych systemów są integrowane zarówno w wewnętrznym systemie analizy dzienników, jak i w systemie wykrywania nieautoryzowanego dostępu.
Dzienniki stanowią najważniejszy komponent ogólnej strategii wykrywania incydentów i reagowania na nie, którą omówiono szczegółowo w części „Zagrożenia bezpieczeństwa — rozpoznawanie, ochrona i reagowanie”.
Zarządzanie utrzymaniem ciągłości działalności biznesowej i odzyskiwaniem awaryjnym
Bardzo dbamy o odporność naszych produktów, także dlatego, że sami — wewnętrznie, w Atlassian — korzystamy z tych samych produktów. Zdajemy sobie sprawę, że zakłócenia mogą się zdarzać. Dlatego z determinacją staramy się uwzględniać procesy planowania na wypadek zakłóceń i postępowania z nimi tak, aby ich wystąpienie miało jak najmniejszy wpływ na naszych klientów. Nasze programy zapewniania ciągłości działalności biznesowej (BC) i odzyskiwania awaryjnego (DR) obejmują różne działania ukierunkowane na osiągnięcie tych celów.
Zaangażowanie kierownictwa w aktywność związaną z planowaniem zapewniania ciągłości działalności biznesowej i odzyskiwania awaryjnego zapewnia nadzór konieczny do przeniesienia odpowiedzialności za odporność na wszystkie zespoły. Celem naszej aktywności związanej z planowaniem zapewniania ciągłości działalności biznesowej i odzyskiwania awaryjnego jest właściwe zrównoważenie kosztów, korzyści i ryzyka poprzez analizę „docelowego czasu odzyskiwania” (RTO) i „docelowych punktów odzyskiwania” (RPO) usług. W wyniku tej analizy utworzyliśmy prosty 4-warstwowy system, który ułatwia pogrupowanie usług w oparciu o ich wymagania dotyczące odzyskiwania. Szczegółowe informacje na temat tego podejścia można znaleźć na stronie Zarządzanie danymi klienta w Atlassian.
Nasze programy zapewniania ciągłości działalności biznesowej i odzyskiwania awaryjnego obejmują następujące aktywności:
1. Uwzględnianie środków zapewniających nadmiarowość w celu spełnienia wymagań związanych z odpornością.
2. Testowanie i weryfikowanie tych środków zapewniających nadmiarowość.
3. Wyciąganie wniosków z testów w celu ciągłego doskonalenia środków zapewniania ciągłości działalności biznesowej i odzyskiwania awaryjnego.
Tworzymy nasze produkty w taki sposób, aby jak najlepiej korzystać z możliwości nadmiarowości, takich jak strefy i regiony dostępności oferowane przez naszych dostawców usług w chmurze.
Nieustannie monitorujemy wiele różnych wskaźników, aby wykrywać potencjalne problemy już na wczesnym etapie. Na podstawie tych wskaźników konfigurowane są alerty używane do powiadamiania inżynierów ds. niezawodności lokalizacji (SRE) lub odpowiednich zespołów inżynierów produktów o naruszeniu wartości progowych, aby mogli podjąć natychmiastowe działania zgodnie z naszym procesem reagowania na incydenty. Inżynierowie SRE odgrywają również kluczową rolę w wykrywaniu luk w programie odzyskiwania awaryjnego i współpracują z naszym zespołem ds. ryzyka i zgodności nad ich wyeliminowaniem. W każdym z naszych zespołów znajduje się również specjalista ds. odzyskiwania awaryjnego, który nadzoruje i pomaga zarządzać aspektami odzyskiwania awaryjnego właściwymi dla danego zespołu.
Nasze testy odzyskiwania awaryjnego obejmują aspekty proceduralne i technologiczne, w tym odpowiednie udokumentowanie procesu. Częstotliwość przeprowadzania testów odzyskiwania awaryjnego zależy od poziomu krytyczności każdej z usług. Przykładowo testowanie procesów tworzenia kopii zapasowych i odzyskiwania w przypadku kluczowych systemów, z których bezpośrednio korzystają klienci, odbywa się co kwartał. Przeprowadzamy testy ręczne i ad-hoc pracy naszych systemów w trybie awaryjnym. Rodzaje testów są różne — od mniej skomplikowanych teoretycznych ćwiczeń symulacyjnych po bardziej złożone testy pracy w trybie awaryjnym na poziomie stref dostępności lub regionalnym. Niezależnie od stopnia złożoności testu, uważnie rejestrujemy i dokumentujemy jego wyniki, analizujemy i wskazujemy możliwe luki lub obszary wymagające poprawy, a następnie doprowadzamy do ich zamknięcia, wykorzystując zgłoszenia Jira. W ten sposób zapewniamy ciągłe doskonalenie całego procesu.
Każdego roku przeprowadzamy oceny wpływu na działalność (Business Impact Assessment, BIA) w celu oszacowania ryzyka związanego z usługami o krytycznym znaczeniu. Wyniki tych ocen BIA pomagają w opracowaniu strategii odzyskiwania awaryjnego i zapewniania ciągłości działalności biznesowej. W rezultacie możemy opracować skuteczne plany odzyskiwania awaryjnego i zapewniania ciągłości działalności biznesowej dla usług o znaczeniu krytycznym.
Dostępność usług
Oprócz wspomnianych powyżej środków, korzystając z własnego produktu Statuspage, udostępniamy naszym klientom w czasie rzeczywistym informacje o stanie dostępności naszych usług. W razie jakichkolwiek problemów z dowolnym z naszych produktów klienci dowiedzą się o tym, gdy tylko do nas samych dotrze taka informacja.
Kopie zapasowe
W Atlassian realizujemy kompleksowy program tworzenia kopii zapasowych. Obejmuje on nasze systemy wewnętrzne, w których mechanizmy tworzenia kopii zapasowych zaprojektowano zgodnie z wymaganiami odzyskiwania systemu. W przypadku produktów Atlassian Cloud, a w szczególności danych klientów i aplikacji, również dysponujemy rozbudowanym mechanizmem tworzenia kopii zapasowych. Atlassian korzysta z funkcji migawki usługi relacyjnej bazy danych Amazon RDS (Relational Database Service) w celu codziennego tworzenia zautomatyzowanych kopii zapasowych każdej instancji RDS.
Migawki Amazon RDS są przechowywane przez 30 dni z obsługą odzyskiwania do określonego momentu i są szyfrowane przy użyciu algorytmu AES-256. Dane kopii zapasowych nie są przechowywane na zewnątrz, tylko replikowane do wielu centrów danych w obrębie konkretnego regionu AWS. Co kwartał przeprowadzamy również testowanie naszych kopii zapasowych.
W przypadku Bitbucket dane są replikowane do innego regionu AWS, a w każdym regionie codziennie wykonywane są niezależne kopie zapasowe.
Nie używamy tych kopii zapasowych do przywracania destrukcyjnych zmian zainicjowanych przez klienta, takich jak pola nadpisane za pomocą skryptów albo usunięte zgłoszenia, projekty lub witryny. W celu uniknięcia utraty danych zalecamy regularne wykonywanie kopii zapasowych. Więcej informacji na temat tworzenia kopii zapasowych można znaleźć w dokumentacji pomocy technicznej danego produktu.
Bezpieczeństwo fizyczne
Zabezpieczenia fizyczne stosowane w naszych biurach wynikają z naszych zasad zapewniania bezpieczeństwa fizycznego i środowiskowego, które gwarantują wdrożenie w naszych środowiskach lokalnych i chmurowych solidnych zabezpieczeń fizycznych. Te zasady obejmują takie dziedziny, jak bezpieczne obszary pracy, zabezpieczenia naszego sprzętu informatycznego, niezależnie od jego lokalizacji, ograniczenie dostępu do naszych budynków i biur do odpowiednich osób, a także monitorowanie fizycznych punktów wejścia i wyjścia. Wśród naszych praktyk zapewniania bezpieczeństwa fizycznego można wskazać obecność pracowników recepcji w godzinach pracy, wymóg rejestrowania gości oraz dostęp do obszarów niepublicznych za pomocą identyfikatorów. Współpracujemy również z kierownictwem naszego budynku biurowego w celu kontroli dostępu po godzinach i monitoringu wizyjnego wejść i wyjść, zarówno głównych, jak i zaopatrzeniowych.
Współpracujące z nami centra danych muszą wykazać zgodność co najmniej z normą SOC 2. Te certyfikaty uwzględniają szereg środków kontroli, w tym ochrony i zabezpieczeń fizycznych oraz środowiskowych. Dostęp do centrów danych jest ograniczony do upoważnionego personelu i sprawdzany przy użyciu biometrycznych mechanizmów weryfikacji tożsamości. Zabezpieczenia fizyczne obejmują ochronę na terenie firmy, monitoring wizyjny w obwodzie zamkniętym, śluzy oraz dodatkowe środki ochrony przed włamaniem.
Zapewnianie bezpieczeństwa danych
Dysponujemy szeregiem środków, które zapewniają bezpieczeństwo i dostępność danych naszych klientów, a także umożliwiają klientom zachowanie kontroli nad tymi danymi w najszerszym możliwym stopniu.
Centra danych
Produkty oraz dane Atlassian są hostowane przez wiodącego w branży dostawcę hostingu w chmurze — Amazon Web Services (AWS). Na skalę globalną wykorzystujemy możliwości zapewniania optymalnej wydajności dzięki opcjom nadmiarowości i pracy w trybie awaryjnym. Korzystamy wielu geograficznie rozproszonych regionów usług AWS (wschodnia i zachodnia część USA, Unia Europejska oraz obszar Azji i Pacyfiku) oraz wielu stref dostępności w każdym z tych regionów. To daje nam pewność, że awaria w pojedynczym centrum danych nie będzie miała wpływu na dostępność naszych produktów lub danych klientów. Więcej informacji można znaleźć w artykule Zarządzanie danymi klienta w Atlassian oraz na stronie Infrastruktura hostingu w chmurze.
Dostęp fizyczny do naszych centrów danych, w których przechowywane są dane klientów, jest ograniczony tylko do osób upoważnionych i weryfikowany przy użyciu środków biometrycznych. Zabezpieczenia fizyczne naszych centrów danych obejmują ochronę na terenie firmy, monitoring wizyjny w obwodzie zamkniętym, śluzy oraz dodatkowe środki ochrony przed włamaniem.
Szyfrowanie danych
Wszystkie dane klientów przechowywane w produktach Atlassian Cloud są szyfrowane w trakcie przesyłania przez sieci publiczne przy użyciu protokołu TLS 1.2+ z doskonałym utajnianiem przekazywania (PFS) w celu ochrony przed nieupoważnionym ujawnieniem lub modyfikacją. Nasza implementacja protokołu TLS wymusza stosowanie silnych szyfrów i odpowiednich długości kluczy, jeśli są obsługiwane przez przeglądarkę.
Dyski serwerowe, na których przechowywane są dane i załączniki klientów korzystających z produktów Jira Software Cloud, Jira Service Management Cloud, Jira, Bitbucket Cloud, Confluence Cloud, Statuspage, Opsgenie, Trello, Loom, Compass i Rovo są w całości szyfrowane podczas magazynowania przy użyciu metody AES-256, będącej standardem w branży. Aktualności na temat naszej platformy można znaleźć na stronie harmonogramu Atlassian Trust.
Zarządzanie kluczami
Atlassian korzysta z usług zarządzania kluczami (KMS) dostawcy usług w chmurze w celu zarządzania kluczami. Do każdego klucza jest przypisany właściciel odpowiedzialny za zapewnienie stosowania odpowiedniego poziomu kontroli zabezpieczeń w przypadku kluczy.
Oddzielenie dzierżawców
Choć klienci używający produktów Atlassian korzystają ze wspólnej chmurowej infrastruktury informatycznej, stosujemy środki zapewniające logiczną separację klientów, tak aby działania jednego klienta nie wpływały na dane ani usługi innych klientów.
Podejście Atlassian do osiągnięcia takiego stanu zależy od rodzaju naszej aplikacji. W przypadku Jira i Confluence Cloud do logicznego odizolowania naszych klientów wykorzystujemy koncepcję nazywaną „kontekstem dzierżawcy”. Implementujemy ją na poziomie kodu aplikacji i zarządzamy przy użyciu opracowanej przez nas usługi o nazwie „Tenant Context Service” (TCS). Założenia tej koncepcji są następujące:
- Podczas magazynowania dane każdego klienta są logicznie oddzielone od innych dzierżawców.
- Wszelkie wnioski przetwarzane przez Jira lub Confluence mają widok „właściwy dla dzierżawcy”, co sprawia, że nie ma on wpływu na innych dzierżawców.
Ogólnie rzecz biorąc działanie usługi TCS opiera się na przechowywaniu „kontekstu” poszczególnych dzierżawców klienta. Kontekst każdego dzierżawcy jest powiązany z unikatowym identyfikatorem przechowywanym centralnie przez usługę TCS i obejmuje szereg metadanych skojarzonych z dzierżawcą (takich jak bazy danych, w których znajduje się dzierżawca; licencje posiadane przez dzierżawcę; funkcje, do których ma on dostęp oraz szereg innych informacji na temat konfiguracji). Gdy klient uzyskuje dostęp do Jira lub Confluence Cloud, usługa TCS używa identyfikatora dzierżawcy, aby zebrać te metadane, które następnie są łączone z dowolnymi operacjami podejmowanymi przez dzierżawcę w aplikacji w trakcie całej sesji.
Kontekst dostarczany przez usługę TCS pełni funkcję „soczewki”, przez którą przepuszczane są wszelkie interakcje z danymi klienta. Ta soczewka jest zawsze przypisana do jednego konkretnego dzierżawcy. Dzięki temu jeden dzierżawca klienta nie ma dostępu do danych innego dzierżawcy ani nie jest w stanie wpłynąć na usługę innego dzierżawcy podejmowanymi przez siebie działaniami.
Więcej informacji na temat naszej architektury chmury można znaleźć w zasobach wsparcia dotyczących chmury.
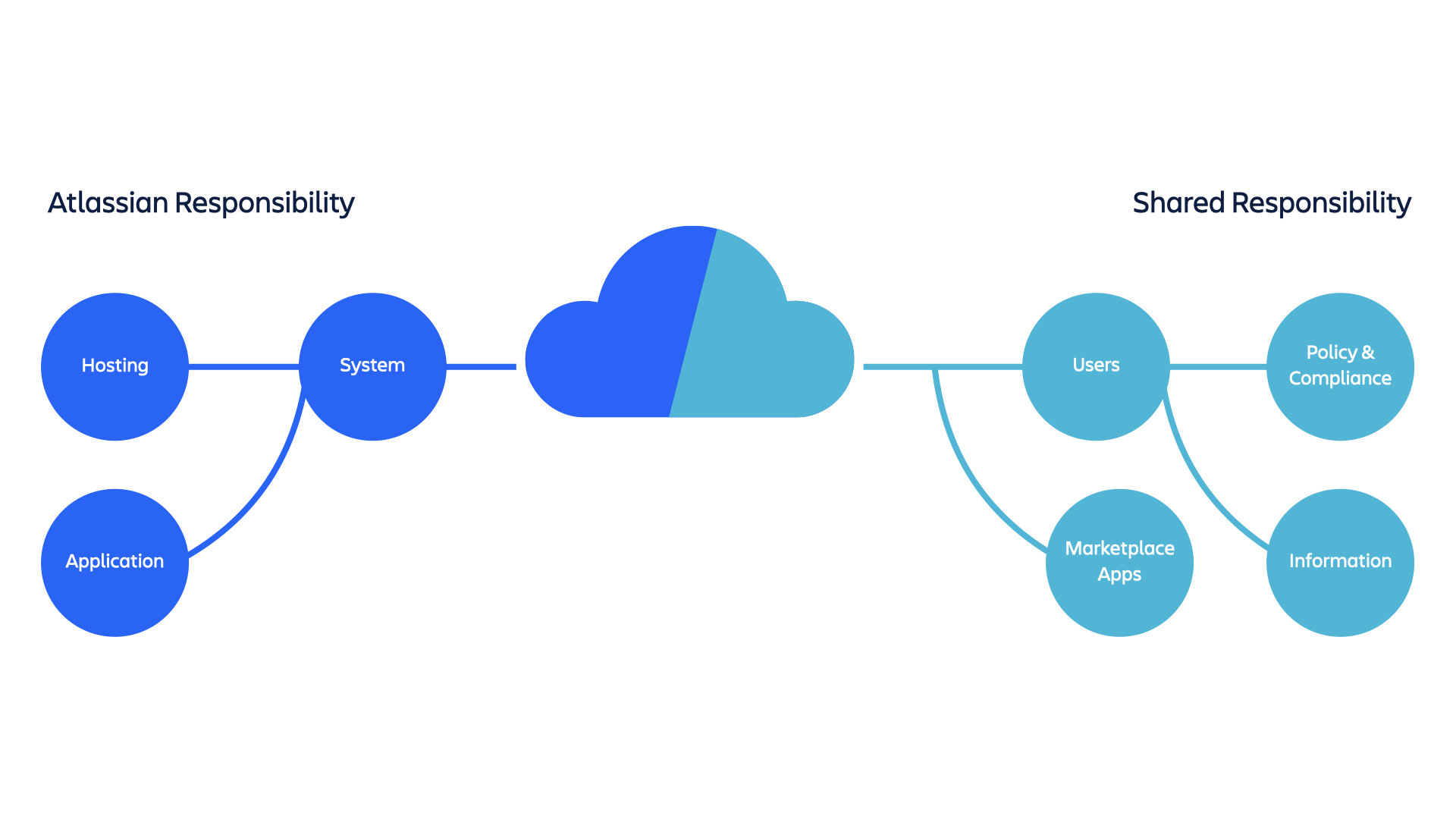
Wspólna odpowiedzialność za zarządzanie danymi klientów
Atlassian odpowiada za zapewnianie bezpieczeństwa, dostępności oraz wydajności udostępnianych aplikacji, systemów, w których one działają, a także środowisk, w których te systemy są hostowane. Jednak zapewnianie bezpieczeństwa jest wspólnym obowiązkiem Atlassian oraz naszych klientów, w szczególności w odniesieniu do czterech następujących obszarów:
Zasady i zgodność
Zapewnienie, że system spełnia potrzeby biznesowe klientów i jest użytkowany z zachowaniem zgodności z wymogami branżowymi, regulacyjnymi i legislacyjnymi.
Użytkownicy
Tworzenie kont użytkowników i zarządzanie nimi.
Informacje
Treści, które klienci przechowują w rozwiązaniach Confluence Cloud, Jira Cloud, Jira Service Management, Trello, Bitbucket Cloud, Compass, Loom lub Rovo.
Aplikacje ze sklepu Marketplace
Usługi stron trzecich, które można zintegrować z produktami Atlassian.
Mimo że Atlassian podejmuje wszelkie konieczne kroki w celu ochrony i zabezpieczenia danych klientów, w rzeczywistości decyzje klientów dotyczące konfiguracji naszych produktów również mają znaczący wpływ na sposób wdrażania zabezpieczeń. Ważne kwestie, o których powinni wiedzieć, używając naszych produktów, to m.in:
- Weryfikacja domeny i centralne zarządzanie kontami użytkowników — administratorzy w organizacjach naszych klientów mogą weryfikować domeny, aby potwierdzić, że są ich właścicielami. Weryfikacja domen umożliwia administratorowi centralne zarządzanie wszystkimi kontami Atlassian pracowników oraz stosowanie zasad uwierzytelniania (w tym wymagań dotyczących haseł oraz protokołu SAML). Jest to ważna czynność i zdecydowanie zalecamy wszystkim naszym klientom jej wykonanie w celu zabezpieczenia dostępu do kont oraz danych dostępnych za ich pośrednictwem.
- Uprawnienia dostępu — nasze produkty zostały od podstaw zaprojektowane tak, aby umożliwiały współpracę, jednak klienci muszą zachować ostrożność podczas przyznawania użytkownikom w swojej organizacji uprawnień zapewniających dostęp do danych. W niektórych przypadkach mogą oni również przyznać dostęp publiczny do danych. Atlassian nie ma nad tym kontroli i w takich przypadkach nie może zapobiec kopiowaniu ani dalszemu rozpowszechnianiu danych.
- Dostęp scentralizowany — zdecydowanie zalecamy naszym klientom korzystanie z usługi Atlassian Guard w celu zapewnienia scentralizowanej administracji i zwiększenia bezpieczeństwa (łącznie z wymuszonym uwierzytelnianiem dwuskładnikowym i logowaniem jednokrotnym) we wszystkich używanych przez nich produktach firmy Atlassian.
Więcej informacji zawiera nasz dokument pt. Wspólne obowiązki związane z zapewnieniem bezpieczeństwa w chmurze.
Kontrola dostępu do danych klientów
Wszystkie dane naszych klientów traktujemy jako równie wrażliwe, dlatego wdrożyliśmy rygorystyczne środki kontroli w zakresie administrowania tymi danymi. W trakcie procesu wdrażania do pracy nasi pracownicy wewnętrzni i podwykonawcy uczestniczą w szkoleniu, którego celem jest zwiększenie świadomości o najlepszych praktykach przetwarzania danych klientów oraz ważności tych praktyk.
W Atlassian dostęp do danych klienta przechowywanych w naszych aplikacjach mają wyłącznie upoważnieni pracownicy Atlassian. Uwierzytelnianie odbywa się za pośrednictwem indywidualnych kluczy publicznych chronionych hasłem, a serwery akceptują wyłącznie połączenia przychodzące SSH z lokalizacji Atlassian i wewnętrznych centrów danych. Dostęp jest ograniczony do grup posiadających odpowiednie uprawnienia, o ile wniosek o dostęp nie zostanie wysłany i pomyślnie zweryfikowany, z wymaganiem dodatkowego uwierzytelniania dwuskładnikowego.
Rygorystyczne kontrole uwierzytelniania i autoryzacji ułatwiają naszemu globalnemu zespołowi wsparcia realizację procesów obsługi i pomocy technicznej. Dostęp do hostowanych aplikacji oraz danych jest uzyskiwany wyłącznie w celu monitorowania stanu aplikacji oraz przeprowadzenia konserwacji systemu lub aplikacji, bądź na wniosek klienta przesłany za pośrednictwem naszego systemu wsparcia.
Aby zapewnić naszym klientom dodatkowe mechanizmy kontroli bezpieczeństwa, zanim nasi inżynierowie pomocy technicznej będą mogli uzyskać dostęp do danych klientów przechowywanych w naszych aplikacjach, nasi klienci muszą wyrazić jednoznaczną zgodę na taki dostęp za pośrednictwem naszego narzędzia Consent Control Checker.
Nieuprawniony lub niewłaściwy dostęp do danych klienta jest traktowany jako incydent dotyczący bezpieczeństwa i objęty procesem zarządzania incydentami. Ten proces uwzględnia instrukcje powiadamiania klientów, których dotyczy incydent, o zaobserwowaniu przypadku naruszenia zasad.
Przechowywanie i usuwanie danych
Wdrożyliśmy odpowiednie przepisy, aby reagować na wnioski użytkowników o usunięcie danych osobowych. Ponadto pomagamy użytkownikom końcowym z kontami Atlassian usuwać swoje dane osobowe. Dysponujemy również narzędziami do importowania i eksportowania, aby nasi klienci mogli korzystać z dostępu do swoich danych oraz importować i eksportować te dane przy użyciu narzędzi Atlassian.
Witryny klientów są dezaktywowane 15 dni po zakończeniu bieżącego okresu subskrypcji klienta. Atlassian przechowuje dane dezaktywowanych witryn przez 15 dni (w przypadku witryn ewaluacyjnych) lub przez 60 dni (w przypadku witryn utworzonych w ramach płatnej subskrypcji) po zakończeniu bieżącego okresu subskrypcji klienta. Należy pamiętać, że w przypadku systemu Jira dane zostaną usunięte tylko wtedy, jeśli użytkownik zrezygnuje z subskrypcji wszystkich subskrybowanych dotychczas produktów Jira.
Dodatkowe informacje można znaleźć na stronie Praktyki dotyczące bezpieczeństwa lub Przechowywanie danych — często zadawane pytania.
Zapewnianie bezpieczeństwa na poziomie osobowym
Dążymy do tego, aby każdy członek naszego personelu wiedział, jak wykonywać swoją pracę w sposób bezpieczny i miał możliwość podejmowania właściwych działań. Zakorzenienie nastawienia na bezpieczeństwo leży u podstaw kultury Atlassian i przyczynia się do podniesienia poziomu ogólnej odporności na potencjalne cyberataki.
Szkolenia zwiększające świadomość w zakresie bezpieczeństwa
Cały zespół Atlassian przechodzi szkolenie uświadamiające z zakresu bezpieczeństwa podczas procesu wdrażania, a następnie corocznie, aby zapewnić świadomość najnowszych zagrożeń bezpieczeństwa i stosowanie bezpiecznych praktyk w swojej pracy.
Rozumiemy, że wiele zagrożeń dla bezpieczeństwa, z którymi zmaga się nasz zespół, pokrywa się z tymi, z którymi borykają się nasi podwykonawcy, dlatego rozszerzamy szkolenia uświadamiające z zakresu bezpieczeństwa, aby objęły one również tych podwykonawców.
Nasz program szkoleń uświadamiających z zakresu bezpieczeństwa dotyczy szeregu zagadnień związanych z bezpieczeństwem, w tym aktualnych zagrożeń dla bezpieczeństwa, ataków i oszustw, identyfikowania i raportowania symulacji phishingu, klasyfikacji danych i zarządzania nimi, ochrony danych klientów oraz identyfikowania i zgłaszania zagrożeń dla bezpieczeństwa. Wszystkie tematy poruszane na naszym szkoleniu uświadamiającym z zakresu bezpieczeństwa są zgodne z naszymi wymaganiami dotyczącymi zgodności i przestrzegania regulacji.
Oprócz ogólnych szkoleń dotyczących bezpieczeństwa informacji, przeznaczonych dla całego zespołu Atlassian, oferujemy specjalistyczne szkolenia dla naszych programistów z zakresu bezpiecznego kodowania i zarządzania lukami w zabezpieczeniach, aby zapewnić naszej firmie i jej klientom bezpieczne wyniki. Zespoły programistyczne są również wspierane przez dedykowanych inżynierów ds. zabezpieczeń w całej organizacji, którzy pomagają w zadaniach operacyjnych związanych z bezpieczeństwem.
Utrzymujemy również otwarte kanały komunikacji, aby wszyscy nasi pracownicy mieli łatwy dostęp do zespołu ds. bezpieczeństwa w celu uzyskania wsparcia.
Program Security Champions
Nasz program Security Champions obejmuje wyznaczenie liderów w dziedzinie zabezpieczeń w każdym z naszych zespołów ds. produktów i usług. Obowiązkiem tego dedykowanego lidera jest promowanie najważniejszych praktyk dotyczących bezpieczeństwa wśród członków zespołu oraz współpraca z naszym centralnym zespołem ds. bezpieczeństwa w sprawie problemów z zabezpieczeniami, aby zapewnić lepszą komunikację.
Nasi liderzy przechodzą zaawansowane szkolenie z zakresu zabezpieczeń aplikacji, aby ułatwić im identyfikowanie luk w zabezpieczeniach, zrozumienie praktyk bezpiecznego programowania i tworzenie bezpiecznego kodu.
Liderzy biorący udział w programie Security Champions firmy Atlassian spotykają się regularnie, aby podzielić się narzędziami oraz wiedzą na temat najnowszych problemów związanych z bezpieczeństwem oraz wyzwań, jakim stawiają czoła. Dzięki temu wszystkie nasze zespoły mogą skorzystać z tych informacji. Program ten służy jako punkt wyjścia do tego, aby bezpieczeństwo stało się jeszcze bardziej integralną częścią naszej kultury.
Sprawdzanie przeszłości pracowników
Chcemy, aby zatrudniane przez nas osoby w pozytywny sposób kształtowały naszą kulturę, której bezpieczeństwo jest integralną częścią. W tym celu sprawdzamy przeszłość wszystkich nowo zatrudnionych w takim stopniu, w jakim umożliwiają to lokalne przepisy. W zależności od roli może to obejmować weryfikację danych dotyczących karalności, wykształcenia i dotychczasowego zatrudnienia, a także analizę kredytową.
Zapewnianie bezpieczeństwa na poziomie naszych produktów
Atlassian koncentruje się na zapewnieniu, że bezpieczeństwo stanowi kluczową część wszystkich faz cyklu życia naszych produktów. Wykorzystujemy w tym celu różne metody.
Karty wyników dotyczących zaufania
Koncentrujemy się na zapewnieniu, aby zaufanie (w tym m.in. bezpieczeństwo, zapobieganie nadużyciom i zgodność) znajdowało się na pierwszym planie w odniesieniu do całego pakietu naszych produktów. W tym celu wdrożyliśmy system odpowiedzialności i monitorowania nazywany „kartami wyników dotyczących zaufania do produktu”, aby mierzyć zaufanie i stan bezpieczeństwa wszystkich produktów w firmie Atlassian. Jest to opracowany przez nas zautomatyzowany proces, w ramach którego na podstawie szerokiej gamy kryteriów (takich jak bieżące luki w zabezpieczeniach, zakres szkoleń, dostosowanie zgodności i ostatnie incydenty dotyczące bezpieczeństwa) wylicza się ogólną punktację stanowiącą ocenę zaufania do każdego z naszych produktów.
Dzięki zastosowaniu takiego procesu ocen każdy z naszych zespołów ds. produktów zyskuje obiektywny pogląd na to, jakie obszary zaufania wymagają uwagi. Proces ten pozwala wykryć istniejące luki, które należy wyeliminować, oraz wskazać działania, jakie należy w tym celu podjąć. Proces tworzenia kart wyników dotyczących zaufania daje również organizacji ds. zaufania Atlassian możliwość monitorowania rozwoju produktów w czasie pod względem zaufania, a w szczególności w miarę skalowania naszego pakietu produktów.
Działania z zakresu bezpieczeństwa
Nasz zespół ds. bezpieczeństwa produktów prowadzi strategiczne działania mające na celu przeprowadzanie okresowych ocen bezpieczeństwa w celu identyfikacji zagrożeń technicznych, zwłaszcza w krytycznych obszarach platformy lub produktów. Głównym rezultatem jest identyfikacja i usuwanie luk w zabezpieczeniach, aby konsekwentnie poprawiać stan bezpieczeństwa naszej platformy lub obszarów produktowych.
Ukierunkowane zapewnianie bezpieczeństwa
Zespół ds. bezpieczeństwa produktów realizuje również proces przeglądu zabezpieczeń w ramach zapewniania bezpieczeństwa na poziomie projektów oprogramowania. Ten oparty na ryzyku proces służy do wyznaczania obszarów priorytetowych, na których powinny skupić się aktywności związane z zapewnianiem bezpieczeństwa, oraz wskazywania działań wymaganych do zniwelowania ryzyka związanego z projektem. W zależności od rozpoznanego poziomu ryzyka aktywności związane z zapewnianiem bezpieczeństwa stanowią kombinację następujących działań:
- modelowanie zagrożeń;
- przegląd projektu;
- przegląd kodu (ręczny i wspomagany narzędziami);
- testowanie zabezpieczeń;
- niezależne zapewnianie bezpieczeństwa z wykorzystaniem zewnętrznych badaczy i konsultantów.
Jak wspomniano w innej części niniejszego artykułu, prowadzimy również wiodący w branży program wykrywania błędów, który polega na bieżącym zapewnianiu bezpieczeństwa z pomocą zaufanej grupy crowdsourcingowej badaczy zabezpieczeń.
Bezpieczne projektowanie poprzez modelowanie zagrożeń
Na etapie planowania i projektowania naszych produktów stosujemy modelowanie zagrożeń, aby lepiej zrozumieć ryzyko dla bezpieczeństwa, jakie występuje, gdy projekty stają w obliczu złożonych zagrożeń lub uwzględniają tworzenie funkcji o znaczeniu krytycznym dla bezpieczeństwa. Tego rodzaju działania obejmują sesje symulacyjne czy burze mózgów z udziałem naszych inżynierów, inżynierów ds. zabezpieczeń, architektów oraz kierowników produktów, mające na celu rozpoznanie adekwatnych zagrożeń i ustalenie ich priorytetu. Te informacje są uwzględniane w procesie projektowania i pozwalają wdrożyć odpowiednie środki kontroli. Modelowanie obejmuje również ukierunkowane przeglądy oraz testy na dalszych etapach prac programistycznych.
Analiza kodu
Dysponujemy platformą do zautomatyzowanej analizy kodu (o nazwie Security Assistant), która obejmuje wszystkie repozytoria kodu w Atlassian. Na tej platformie działa wiele narzędzi do analizy statystycznej (stale rozwijanych i doskonalonych), które przyczyniają się do zwiększenia ogólnego poziomu bezpieczeństwa naszego kodu. Za każdym razem po utworzeniu pull requestu w repozytorium platforma:
- wyszukuje i identyfikuje przestarzałe zależności kodu, które mogą być źródłem luk w zabezpieczeniach (omówiono je szczegółowo w tej części niniejszego artykułu, która dotyczy naszego podejścia do zarządzania lukami w zabezpieczeniach);
- identyfikuje każde przypadkowe lub niezamierzone ujawnienie tajnych informacji w repozytoriach kodu (np. tokenów uwierzytelniania lub kluczy kryptograficznych);
- przeprowadza analizę w celu wykrycia wszelkich problematycznych wzorców kodowania, które mogłyby prowadzić do powstania luk w zabezpieczeniach naszego kodu.
Baza wiedzy na temat bezpieczeństwa
Aby zagwarantować, że tworzone przez nas produkty są możliwie jak najbezpieczniejsze, zapewniamy naszym programistom dostęp do wsparcia, którego potrzebują, aby stale wzbogacać swoją wiedzę na temat istotnych problemów dotyczących bezpieczeństwa i zagrożeń, jakie muszą mieć na uwadze. W związku z tym prowadzimy wewnętrzną bazę wiedzy dotyczącą bezpieczeństwa aplikacji, z której nasi programiści mogą korzystać w razie potrzeby.
Zagrożenia dla bezpieczeństwa — rozpoznawanie, ochrona i reagowanie
testowanie zabezpieczeń;
Nasze podejście do testowania zabezpieczeń koncentruje się wokół koncepcji „ustawicznego zapewniania bezpieczeństwa” — nie tylko przeprowadzamy ukierunkowane, doraźne testy penetracyjne, ale także wdrażamy model ciągłego testowania oparty na crowdsourcingowym programie wykrywania błędów. Jesteśmy przekonani, że takie wielopłaszczyznowe podejście znacznie zwiększa szansę wykrycia luk w zabezpieczeniach i dostarczenia naszym klientom możliwie jak najlepiej zabezpieczonych produktów. Więcej informacji można znaleźć w odrębnym artykule dotyczącym naszego podejścia do zewnętrznych testów zabezpieczeń. Poniżej przedstawiono podsumowanie stosowanych przez nas metod testowania, na które składają się:
- Przeglądy zabezpieczeń Atlassian — Jak wspomniano powyżej, nasz zespół ds. bezpieczeństwa produktów realizuje program przeglądu zabezpieczeń, w ramach którego regularnie przeprowadzane są testy zabezpieczeń. Testy składają się z przeglądu kodu oraz testowania zabezpieczeń aplikacji ze szczególnym uwzględnieniem obszarów słabości ujawnionych w ocenie ryzyka.
- Zespół Atlassian ds. testowania zabezpieczeń — Nasz wewnętrzny zespół ds. testów penetracyjnych stosuje podejście oparte na ryzyku, aby przeprowadzić białoskrzynkowe oceny zabezpieczeń (z dostępem do kodu i wsparciem inżynierów) w poszczególnych obszarach działalności (niezależnie od tego, czy chodzi o nasze środowiska chmurowe, nowe produkty lub funkcje, czy wewnętrzne systemy i narzędzia). Współpracujemy również ze specjalistycznymi firmami konsultingowymi zajmującymi się bezpieczeństwem w celu przeprowadzenia białoskrzynkowych testów penetracyjnych na naszych produktach i infrastrukturze.
- Zespół Red Team Atlassian — Powołaliśmy wewnętrzny zespół Red Team odpowiedzialny za symulowanie wrogich ataków mających na celu wykrycie i wykorzystanie luk w zabezpieczeniach naszych systemów, procesów i środowisk, aby umożliwić jak najszybsze ich rozpoznawanie i wyeliminowanie.
- Program wykrywania błędów — korzystamy również z pomocy społeczności platformy Bugcrowd skupiającej zaufanych badaczy zabezpieczeń, wśród której prowadzimy nasz uznany program wykrywania błędów. Dzięki temu możemy w sposób ciągły wykrywać luki w zabezpieczeniach naszych produktów. Z czasem doprowadzi to do zwiększenia kosztu znajdowania i wykorzystywania tych luk dla potencjalnych autorów ataków. Nasz program wykrywania błędów wielokrotnie uznano za najlepszy w branży. Obejmuje on ponad 25 spośród naszych produktów i środowisk — od produktów serwerowych, poprzez aplikacje mobilne, aż po produkty Cloud.
Wszelkie luki w zabezpieczeniach wskazane w poniższych raportach są śledzone w naszym wewnętrznym systemie Jira od momentu ich zgłoszenia w ramach programu wykrywania błędów, a wszelkie ustalenia wynikające z programu wykrywania błędów będą klasyfikowane i monitorowane zgodnie z naszym docelowym poziomem świadczenia usług (SLO) dotyczącym luk w zabezpieczeniach.
- Pobierz najnowszy raport o wykrywaniu błędów Atlassian (grudzień 2025 r.)
- Pobierz najnowszy raport o wykrywaniu błędów Jira Align (grudzień 2025 r.)
- Pobierz najnowszy raport o wykrywaniu błędów Opsgenie (grudzień 2025 r.)
- Pobierz najnowszy raport o wykrywaniu błędów Statuspage (grudzień 2025 r.)
- Pobierz najnowszy raport o wykrywaniu błędów Trello (grudzień 2025 r.)
Zarządzanie lukami w zabezpieczeniach
Atlassian nieustannie pracuje nad zmniejszeniem istotności i częstotliwości występowania luk w zabezpieczeniach swoich produktów, usług i infrastruktury. Dba także o jak najszybsze usuwanie zidentyfikowanych luk. W tym celu wdrożyliśmy wielopłaszczyznowe i stale rozwijane podejście do zarządzania lukami w zabezpieczeniach, które obejmuje zarówno zautomatyzowane, jak i ręczne procesy identyfikowania, śledzenia i usuwania luk w naszych aplikacjach i infrastrukturze.
Identyfikujemy luki w zabezpieczeniach, korzystając z wielu różnych źródeł, takich jak zautomatyzowane skanery, wewnętrzne przeglądy zabezpieczeń, zgłoszenia klientów oraz nasz publiczny program wykrywania błędów. Po zidentyfikowaniu luki zgłoszenie jest rejestrowane w naszym dedykowanym, ogólnofirmowym projekcie śledzenia luk w systemie Jira i przypisywane do odpowiedniego właściciela systemu lub zespołu inżynierów. Nasze scentralizowane podejście pozwala nam wykorzystać narzędzia automatyzacji w celu zapewnienia proaktywnych powiadomień, automatycznych eskalacji oraz raportowania w całym przedsiębiorstwie, aby zagwarantować, że luki są usuwane na czas.
Więcej informacji można znaleźć w artykule na temat podejścia Atlassian do zarządzania lukami w zabezpieczeniach.
Infrastruktura
Korzystamy z gamy narzędzi do wykrywania luk w zabezpieczeniach, które są używane regularnie w naszej infrastrukturze w celu automatycznego skanowania w poszukiwaniu luk i ich rozpoznawania. Korzyści z tych elementów to między innymi:
- Skanowanie sieci — przeprowadzane w celu identyfikowania aktywnych usług, otwartych portów oraz aplikacji działających w naszym środowisku, a także wszelkich luk w zabezpieczeniach na poziomie sieci.
- Ciągłe odnajdowanie zasobów — przeprowadzamy ciągłe odnajdowanie zasobów oraz ciągłą analizę zabezpieczeń w obwodach zewnętrznych naszych sieci. Dysponujemy również wewnętrznie opracowanym mechanizmem inwentaryzacji i odnajdowania zasobów.
- Monitorowanie konfiguracji AWS — monitorujemy konfigurację naszych środowisk AWS pod kątem zgodności z ustalonymi parametrami bazowymi.
Stale analizujemy najnowsze dostępne narzędzia i dodajemy je do pakietu, z którego korzystamy, jeśli tylko uważamy, że ułatwią nam one wykrywanie luk w zabezpieczeniach.
Produkty
W ramach naszego procesu programistycznego, oprócz wspomnianego wcześniej programu wykrywania błędów, wykorzystujemy szereg narzędzi, które pozwalają nam wykryć i wyeliminować możliwie jak najwięcej luk w zabezpieczeniach oraz błędów w naszych produktach, zanim jeszcze zostaną one udostępnione klientom i użytkownikom. Korzystamy z platformy, która ułatwia nam wdrażanie tych narzędzi w naszych repozytoriach kodu. Oto kilka przykładów:
- Atlassian wdraża wiele spośród swoich usług przy użyciu obrazów kontenera Docker. Te obrazy zapewniają spakowane, niezależne środowisko, w skład którego wchodzą odpowiednie biblioteki systemowe, narzędzia, ustawienia konfiguracji oraz wszelkie inne zależności wymagane do uruchomienia naszych produktów, niezależnie od parametrów konfiguracji konkretnego komputera. Włączyliśmy proces pełnego skanowania zabezpieczeń kontenera do pipeline'u CI/CD w przypadku każdego kontenera wdrażanego w naszych środowiskach programistycznych, przejściowych lub produkcyjnych.
- Nasze produkty i usługi opierają się na licznych bibliotekach open source. Korzystając z kombinacji narzędzi opracowanych wewnętrznie, open source i komercyjnych, przeprowadzamy skanowanie w celu wykrycia zależności i porównania ich z bazą danych znanych luk w zabezpieczeniach.
Ponadto, jeśli w trakcie standardowego korzystania z produktu jeden z naszych użytkowników wykryje lukę w zabezpieczeniach, przyjmujemy powiadomienia i niezwłocznie podejmujemy działania w związku z przesłanymi informacjami. Na bieżąco informujemy taką osobę o postępach analizy i reakcji na zgłoszenie.
W niniejszym artykule wspomnieliśmy już wcześniej o procesie „Peer Review, Green Build” (PRGB). Polega on na tym, że każda zmiana w kodzie produktu jest sprawdzana przez co najmniej jedną inną osobę w celu wykrycia ewentualnych problemów, jakie zmiana ta mogłaby potencjalnie spowodować.
Mamy udokumentowane zasady usuwania błędów, które określają ramy czasowe rozwiązywania problemów z zabezpieczeniami naszych produktów, w zależności od poziomu istotności błędu.
Więcej informacji na temat zasad usuwania błędów można znaleźć tutaj. Informacje na temat ostatnio usuniętych błędów oraz błędów, nad usunięciem których aktualnie pracujemy w różnych produktach, można znaleźć w naszym publicznym module śledzenia błędów.
Reagowanie na incydenty
Firma Atlassian stosuje kompleksowe podejście incydentów dotyczących bezpieczeństwa. Pod pojęciem incydentu dotyczącego bezpieczeństwa rozumiemy dowolny incydent wywierający negatywny wpływ na poufność, integralność lub dostępność danych klientów, danych Atlassian lub usług Atlassian.
Mamy wyraźnie zdefiniowane wewnętrzne zasady ramowe, które zawierają udokumentowane porady strategiczne dotyczące różnego rodzaju incydentów. Te zasady obejmują kroki, jakie musimy podejmować na każdym etapie reagowania na incydenty, aby zapewnić spójność, powtarzalność i efektywność naszych procesów. Można wśród nich wymienić wykrywanie i analizę, kategoryzację, powstrzymywanie eskalacji oraz eliminowanie incydentów, a także przywracanie pracy po ich wystąpieniu. Uzyskanie takiej spójności ułatwia zastosowanie naszych własnych produktów, w tym Confluence, Jira i Bitbucket, w ramach naszych procesów reagowania na incydenty:
- Rozwiązanie Confluence służy do tworzenia, dokumentowania i aktualizowania naszych procesów reagowania w centralnej lokalizacji.
- System Jira jest używany do tworzenia zgłoszeń w celu śledzenia postępów procesu reagowania na incydenty związane z bezpieczeństwem (potencjalne i rzeczywiste) od początku do końca.
- Aplikację Bitbucket wykorzystujemy w sytuacjach, gdy tworzymy rozwiązania na bazie kodu. Służą one do reagowania na konkretne skrajne problemy, jakie mają miejsce w przypadku pewnych rodzajów incydentów.
Wprowadziliśmy kompleksowe i scentralizowane dzienniki oraz monitorowanie naszych produktów i infrastruktury, aby umożliwić szybkie wykrywanie potencjalnych incydentów. Cały proces jest wspierany przez zespół wysoce wykwalifikowanych menedżerów ds. incydentów pełniących dyżury domowe, którzy posiadają bogate doświadczenie w koordynowaniu skutecznych reakcji. Mamy również dostęp do szeregu ekspertów zewnętrznych, którzy pomagają nam w badaniu incydentów i możliwie jak najbardziej efektywnym reagowaniu.
Dysponujemy procesami powiadamiania naszych klientów o wystąpieniu potwierdzonych incydentów z udziałem ich danych. Stosujemy także wydajną procedurę przeglądów po incydentach, która pozwala nam wyciągać wnioski z zaistniałych incydentów i doskonalić nasze praktyki w celu utrudnienia autorom złośliwych ataków działania w przyszłości. Więcej informacji można znaleźć w odrębnym artykule pt. Nasze podejście do zarządzania incydentami związanymi z bezpieczeństwem, który jest dostępny w Atlassian Trust Center.
Program detekcji naruszeń zabezpieczeń
Mając na uwadze potrzebę korzystania z naszego podejścia do zarządzania incydentami w kontekście coraz bardziej złożonych zagrożeń, wprowadziliśmy „program reguł wykrywania naruszeń zabezpieczeń”. Reguły wykrywania mają za zadanie ciągle monitorować środowisko Atlassian w celu wykrywania szkodliwej aktywności wobec firmy Atlassian i jej klientów oraz przekazywania alertów na platformę Atlassian do zarządzania incydentami i zdarzeniami z zakresu bezpieczeństwa.
Nasz zespół ds. reguł wykrywania regularnie tworzy nowe reguły wykrywania, dostosowując i doskonaląc istniejące oraz automatyzując reakcje. Te czynności mają charakter wielowymiarowy, obejmując różne produkty, rodzaje ataków i źródła dzienników, aby zasięg naszych reguł wykrywania był możliwie jak najbardziej skuteczny i kompleksowy.
Program ma na celu nie tylko przygotować nas na zagrożenia, w obliczu których stajemy już dziś, ale także w dostatecznym stopniu przewidzieć zagrożenia, które mogą pojawić się w przyszłości, i przygotować nas na ich nadejście. Nasz zespół ds. automatyzacji zabezpieczeń opracował również narzędzie do standaryzacji tworzonych przez nas reguł wykrywania, aby zapewnić wysoki poziom ich spójności i jakości. Sądzimy, że jest to pierwsze tego typu rozwiązanie w branży.
Aby uzyskać więcej informacji na temat naszego programu detekcji naruszeń zabezpieczeń, odwiedź tę stronę.
Program Red Team
Misją zespołu Atlassian Red Team jest ciągłe zwiększanie odporności Atlassian na zaawansowane ataki. Działając z perspektywy autora ataku, jego członkowie odkrywają techniczne, fizyczne i społeczne luki w zabezpieczeniach oraz sprawdzają zdolność naszych zespołów do reagowania w rzeczywistych warunkach. Takie podejście pozwala nam opracowywać i wdrażać skuteczne poprawki zabezpieczeń w środowisku Atlassian. Dzięki temu Atlassian może z większą łatwością oceniać zagrożenia, chronić zasoby i odpowiednio reagować na rzeczywiste ataki.
Zespół Red Team w Atlassian koncentruje się na pełnozakresowej emulacji złośliwych działań. Działamy jak osoby atakujące, których celem są firmy, i staramy się infiltrować i naruszać zabezpieczenia krytycznych systemów. Następnie powiadamiamy osoby zaangażowane i wspólnie wdrażamy długoterminowe, zrównoważone rozwiązania mające na celu wyeliminowanie wykrytych luk w zabezpieczeniach.
- Mierzenie i poprawa skuteczności programu wykrywania i reagowania
- Tworzenie istotnej, korzystnej zmiany stanu i możliwości zabezpieczeń Atlassian.
- Zwiększanie poziomu wiedzy na temat luk w zabezpieczeniach i możliwości reagowania na rzeczywiste ataki.
Zapewnianie bezpieczeństwa partnerom naszego ekosystemu i łańcucha dostaw
Zarządzanie ryzykiem dostawców
Gdy Atlassian angażuje dostawców zewnętrznych (w tym podwykonawców i dostawców usług w chmurze), staramy się, aby takie działania w żaden sposób nie narażały na ryzyko naszych klientów ani ich danych. W związku z tym każdy proponowany angaż dostawcy zewnętrznego jest poddawany analizie przeprowadzanej przez nasz zespół prawny i zespół ds. zaopatrzenia. Jeśli zostanie stwierdzone, że zaangażowanie wiąże się ze średnim, wysokim lub krytycznym ryzykiem, zespoły ds. bezpieczeństwa, zgodności i ryzyka oraz zespół prawny przeprowadzają dodatkowe oceny ryzyka. Z należytą starannością przeprowadzane są również kolejne weryfikacje — podczas odnawiania umowy lub okresowo, w zależności od poziomu ryzyka, jakie stwarza zaangażowanie dostawcy.
Ponadto Atlassian wymaga od dostawców spełnienia minimalnych wymagań dotyczących bezpieczeństwa w ramach ich współpracy z nami. Są one egzekwowane poprzez włączenie ich do naszych umów z dostawcami. Te wymagania różnią się w zależności od poziomu ryzyka przedsięwzięcia i obejmują:
- integrację protokołu SAML2.0/SSO z platformą logowania jednokrotnego Atlassian;
- szyfrowanie danych podczas przesyłania i magazynowania przy użyciu aktualnych algorytmów;
- wdrożenie mechanizmów rejestrowania wystarczających do udostępnienia Atlassian istotnych informacji dotyczących potencjalnych incydentów związanych z bezpieczeństwem.
Atlassian Marketplace
Atlassian Marketplace jest platformą, na której użytkownicy naszych produktów mogą zakupić aplikacje rozszerzające ich funkcjonalność lub pozwalające połączyć je z narzędziami stron trzecich. Większość aplikacji dostępnych w sklepie Marketplace opracowali programiści z podmiotów zewnętrznych, jednak Atlassian podejmuje szereg kroków w celu zapewnienia, aby bezpieczeństwo nadal stanowiło centralny element ekosystemu Marketplace. Należą do nich:
Program wykrywania błędów w sklepie Marketplace — Firma Atlassian wdrożyła w sklepie Marketplace najlepszy w swojej klasie program wykrywania błędów, aby zwiększyć bezpieczeństwo i wiarygodność wszystkich oferowanych tam aplikacji. Uczestniczący w nim partnerzy Marketplace mogą aktywnie przeciwdziałać zagrożeniom dla bezpieczeństwa jeszcze przed ich wystąpieniem, zachęcając badaczy do wykrywania luk w zabezpieczeniach. Aby uzyskać odznakę Cloud Fortified lub Cloud Security Participant, aplikacje muszą uczestniczyć w tym programie. Dowiedz się więcej
Ecoscanner — Platforma Atlassian Ecoscanner umożliwia przeprowadzanie na bieżąco kontroli zabezpieczeń we wszystkich aplikacjach chmurowych w sklepie Marketplace. Dzięki platformie Ecoscanner Atlassian stale monitoruje wszystkie aplikacje chmurowe ze sklepu Marketplace pod kątem typowych luk w zabezpieczeniach, aby zapewnić bezpieczeństwo ekosystemu. Dowiedz się więcej
Program ujawniania luk w zabezpieczeniach — Program ten zapewnia kolejny kanał umożliwiający klientom lub badaczom zabezpieczeń zgłaszanie luk w aplikacjach chmurowych firmie Atlassian i partnerom Marketplace. Atlassian prowadzi ten program i definiuje parametry pozwalające na ograniczenie zagrożeń bezpieczeństwa we wszystkich aplikacjach chmurowych. Dowiedz się więcej
Wymagania dotyczące bezpieczeństwa aplikacji w chmurze — Firma Atlassian zdefiniowała minimalny zestaw wymagań, jakie muszą spełniać wszystkie aplikacje ze sklepu Marketplace. Te wymagania są obligatoryjne i mają na celu wyegzekwowanie stosowania najlepszych praktyk związanych z bezpieczeństwem we wszystkich aplikacjach. Dowiedz się więcej
Zasady usuwania błędów zabezpieczeń — W celu zapewnienia bezpieczeństwa wszystkich aplikacji w ekosystemie Atlassian każdy partner Marketplace jest zobowiązany do przestrzegania umów SLA dotyczących usuwania błędów zabezpieczeń w przypadku każdej aplikacji dostępnej w sklepie Atlassian Marketplace. Po wykryciu luki w zabezpieczeniach partnerzy są zobligowani do jej usunięcia w odpowiednim czasie. Dowiedz się więcej
Karta prywatność i bezpieczeństwo — Aby zwiększyć zaufanie do Marketplace i poprawić widoczność wskaźników bezpieczeństwa, karta Prywatność i bezpieczeństwo została wprowadzona do interfejsu użytkownika oferty Marketplace dla aplikacji w chmurze. Karta Prywatność i bezpieczeństwo zawiera szczegółowe informacje na temat prywatności, bezpieczeństwa, przetwarzania danych i praktyk zgodności w odniesieniu do aplikacji w chmurze. Ponieważ program samodzielnej oceny bezpieczeństwa (SSA) został wycofany 22 sierpnia 2023 r., karta Prywatność i bezpieczeństwo zastąpiła SSA jako wymóg Cloud Fortified. Dowiedz się więcej
Więcej informacji na temat naszego podejścia do bezpieczeństwa w sklepie Marketplace można znaleźć w witrynie Centrum zaufania Atlassian Marketplace.
Zarządzanie zgodnością i ryzykiem
Nasze programy zarządzania zasadami i ryzykiem
Firma Atlassian wdrożyła program zarządzania zaufaniem Trust Management Program (TMP) oparty na normie ISO 27001 — Systemy zarządzania bezpieczeństwem informacji. Ten program bierze pod uwagę potrzeby naszych klientów w zakresie bezpieczeństwa i oferuje zestaw unikatowych dla Atlassian wymagań dotyczących bezpieczeństwa, uwzględniając przy tym środki kontroli wymieniane w różnych międzynarodowych normach bezpieczeństwa.
Następnie rozważamy, czy te środki kontroli są odpowiednie w kontekście konkretnego środowiska i firmy, oraz dobieramy najlepszy sposób ich wdrożenia. Nasz program TMP opiera się na kilku filarach, do których należą:
- Nasz program zarządzania zasadami (PMP) — program zarządzania zasadami stanowi podstawę programu zarządzania zaufaniem. Składa się on z szeregu zasad dotyczących bezpieczeństwa obejmujących domeny wskazane zarówno w normie ISO 27001, jak i w tabeli środków kontroli w chmurze Cloud Controls Matrix (CCM) opracowanej przez organizację Cloud Security Alliance. Opracowane przez nas zasady dotyczące bezpieczeństwa są udostępniane wewnętrznie wszystkim naszym zespołom, aby ich członkowie rozumieli wymagania, jakie muszą spełniać pod względem bezpieczeństwa. Zasady są aktualizowane co roku, a w szczególności w przypadku zaobserwowania nowych zagrożeń i obszarów ryzyka, które wymuszają zmodyfikowanie naszego podejścia do bezpieczeństwa. Fragmenty naszych zasad dotyczących technologii można znaleźć tutaj.
- Nasz program zarządzania ryzykiem (RMP) — nasze środowiska oraz produkty poddajemy ciągłej ocenie ryzyka, aby móc dokonać ewaluacji tych obszarów ryzyka, z którymi aktualnie się borykamy, oraz zapewnić środki kontroli konieczne do skutecznego zarządzania tym ryzykiem. Sposób przeprowadzania tych ocen ryzyka będzie się różnić w zależności od środowiska/produktu poddawanego ocenie. Przykładowo w przypadku naszych produktów często będzie to ocena ryzyka technicznego lub analiza kodu. Bierzemy jednak pod uwagę i staramy się ujawniać także obszary ryzyka biznesowego wyższego poziomu. W ramach naszego programu zarządzania ryzykiem w przedsiębiorstwie przeprowadzamy doroczną ocenę ryzyka i nie rzadziej niż co trzy miesiące wdrażamy projekty mające na celu eliminowanie wykrytych obszarów ryzyka. Więcej informacji na temat naszego podejścia do zarządzania ryzykiem w przedsiębiorstwie można znaleźć w Atlassian Trust Center.
W ramach naszego programu TMP przeprowadzamy cotygodniowe przeglądy stanu zgodności i organizujemy inne wewnętrznie udokumentowane spotkania, aby zagwarantować ciągłość jego efektywnej realizacji.
Zgodność z prawem, przepisami i normami
Nasz program zapewniania bezpieczeństwa został opracowany i wdrożony zgodnie z szeregiem norm branżowych. Przestrzeganie uznanych standardów branżowych jest głównym aspektem naszej strategii bezpieczeństwa, ponieważ zdajemy sobie sprawę, że stanowią one dla naszych klientów niezależne potwierdzenie zgodności programu zabezpieczeń Atlassian z podstawowym zestawem mechanizmów kontroli bezpieczeństwa.
Przestrzegamy kilku kluczowych standardów, w tym:
| ISO 27001 | Podstawą normy ISO 27001 jest opracowanie i wdrożenie systemu zarządzania bezpieczeństwem informacji (ISMS), a następnie wdrożenie pakietu środków kontroli wskazanych w Załączniku A do normy ISO 27001 oraz zarządzanie tymi środkami za pośrednictwem systemu ISMS. Norma ISO/IEC 27018 jest kodeksem praktyk, który zapewnia dodatkowe wskazówki dotyczące wdrażania odpowiednich środków kontroli przewidzianych w normie ISO/IEC 27002 w celu ochrony identyfikowalnych danych osobowych (PII) w środowiskach chmurowych. |
| PCI-DSS | Płacąc kartą kredytową za produkty lub usługi Atlassian, możesz mieć pewność, że dołożymy należytych starań, aby transakcja przebiegła bezpiecznie. Atlassian jest akceptantem spełniającym wymagania normy PCI-DSS. |
| CSA CCM/STAR | Prowadzony przez organizację CSA rejestr Security, Trust & Assurance Registry (STAR) jest bezpłatnym, publicznie dostępnym rejestrem dokumentującym środki kontroli bezpieczeństwa zapewniane przez różne oferty chmury obliczeniowej. Kwestionariusz CSA STAR poziomu 1 w przypadku firmy Atlassian jest dostępny do pobrania na stronie rejestru STAR Cloud Security Alliance. |
| SOC2 | Te raporty pomagają naszym klientom oraz ich audytorom zrozumieć środki kontroli ustanowione w celu wspierania działań i zapewniania zgodności w Atlassian. Wiele produktów Atlassian uzyskało certyfikaty SOC 2. |
| RODO | Zdajemy sobie sprawę, że nasi klienci muszą spełniać wymagania wynikające z rozporządzenia o ochronie danych osobowych (RODO), na które bezpośrednio wpływa sposób korzystania przez nich z produktów i usług Atlassian. W związku z tym przeznaczyliśmy znaczne zasoby na pomaganie naszym klientom w spełnieniu stawianych przed nimi wymagań wynikających z rozporządzenia RODO. Więcej informacji na temat naszego podejścia do zgodności z rozporządzeniem RODO można znaleźć na stronie dotyczącej zgodności Atlassian z RODO. |
| FedRAMP | Federalny program zarządzania ryzykiem i autoryzacją (Federal Risk and Authorization Management Program, FedRAMP) to federalny program rządowy Stanów Zjednoczonych, który ma na celu utworzenie znormalizowanego podejścia do oceny bezpieczeństwa, autoryzacji i ciągłego monitorowania produktów i usług w chmurze. Zobacz indywidualny status następujących produktów Atlassian w witrynie FedRAMP Marketplace:
|
Oprócz informacji podanych powyżej, na naszej stronie programu zgodności dostępna jest obszerna lista norm branżowych, których przestrzegamy.
Ochrona prywatności w Atlassian
Firma Atlassian wdrożyła kompleksowy i globalny program ochrony prywatności, aby zapewnić spełnienie przez nas zobowiązań dotyczących ochrony danych i prywatności. Stosujemy nasze zasady prywatności przy opracowywaniu naszych produktów i korzystaniu z nich, w tym przez uwzględnianie ochrony prywatności zawsze już w fazie projektowania.
-
Przejrzystość: staramy się utrzymać zaufanie, stosując przejrzyste zasady. Informacje na temat naszych praktyk dotyczących prywatności i kluczową dokumentację na temat prywatności (w tym naszą Politykę prywatności i Załącznik dotyczący przetwarzania danych) można znaleźć w naszym centrum Trust Center i w naszych Informacjach prawnych.
-
Ocena wpływu transferu danych: przekazujemy informacje, aby pomóc naszym klientom przeprowadzić ocenę wpływu transferu danych w związku z korzystaniem przez nich z naszych produktów. Nasza ocena wpływu transferu danych jest dostępna tutaj.
-
Mechanizmy kontroli dostępu i szkolenia: pracownicy Atlassian, którzy mają dostęp do danych osobowych lub je przetwarzają, zostali przeszkoleni w zakresie postępowania z tymi danymi oraz są zobowiązani do zapewnienia ich poufności i bezpieczeństwa.
-
Narzędzia do zarządzania danymi: zapewniamy naszym klientom narzędzia pomagające im w wypełnianiu obowiązków w zakresie ochrony prywatności związane z wnioskami osób, których dane dotyczą, w tym prawa do usunięcia danych i prawa do dostępu. Informacje o naszych narzędziach i procesach zarządzania danymi można znaleźć tutaj.
-
Aktualności i aktualizacje: aby otrzymywać od nas powiadomienia o aktualizacjach naszych warunków prawnych i naszej listy podwykonawców, możesz zasubskrybować tutaj.
Audyt wewnętrzny i zewnętrzny
W ramach naszych corocznych audytów zgodności (np. SOX, SOC2) przeprowadzamy kompleksowe kontrole bezpieczeństwa, obejmujące niezależną ocenę przez zewnętrzne firmy audytorskie. Dodatkowo przeprowadzamy wewnętrzne audyty operacyjne w obszarach uznawanych za obszary wysokiego ryzyka, do których należą różnorodne zagadnienia związane z bezpieczeństwem. Wyniki audytu są przekazywane komitetowi ds. audytu w naszym zarządzie oraz włączane do cyklu ciągłego doskonalenia, który pomaga nam stale poprawiać jakość programu zapewniania bezpieczeństwa.
Wnioski organów ścigania i administracji publicznej o udostępnienie danych
W ramach działań, jakie podejmujemy, aby zdobyć i utrzymać zaufanie swoich klientów, publikujemy coroczny Raport Atlassian na temat przejrzystości, który zawiera informacje o otrzymanych wnioskach administracji publicznej o udostępnienie danych użytkowników, jak również o usunięcie treści bądź zawieszenie kont użytkowników.
Atlassian odpowiada na wnioski składane przez organy administracji publicznej zgodnie z Polityką prywatności, Umową z klientem, Zasadami dopuszczalnego użytkowania oraz wszelkimi warunkami dotyczącymi konkretnych produktów. Dodatkowe informacje na temat naszych zasad i procedur udzielania odpowiedzi na wnioski o udostępnienie danych użytkowników można znaleźć również w naszych Wytycznych dotyczących wniosków organów ścigania. Udzielając odpowiedzi na dowolny wniosek organu administracji publicznej (o udostępnienie danych użytkowników lub usunięcie kont bądź treści użytkowników), Atlassian przestrzega następujących zasad przewodnich:
-
Zgodnie z naszą wartością Atlassian „Nie #@!% klienta”, Atlassian dokładnie bada wszystkie wnioski organów administracji publicznej dotyczące danych naszych klientów, w tym kwestionując ważność wniosku oraz wszelkie wnioski zgodnie z prawem, w tym wnioski niejasne, zbyt ogólne lub niewłaściwie dostarczone.
-
Agencja rządowa składająca wniosek musi najpierw podjąć próbę uzyskania informacji bezpośrednio od klientów lub użytkowników będących przedmiotem zainteresowania.
-
O ile nie zabrania tego prawo, Atlassian powiadomi klientów o wszelkich wnioskach organów administracji publicznej dotyczących ich danych, aby nasi klienci mieli możliwość zakwestionowania procesu prawnego, zgodnie z naszymi Zasadami powiadamiania użytkowników.
-
W mało prawdopodobnym przypadku konieczności zastosowania się przez firmę Atlassian do wniosku organu administracji publicznej Atlassian odpowie na konkretny wniosek zgodnie z obowiązującym prawem (w tym ustawą Stored Communications Act) i w sposób jak najbardziej ścisły.
-
Atlassian będzie w dalszym ciągu opowiadać się za reformami, które pozwolą nam zapewnić większą przejrzystość względem naszych klientów.
Dalsze pytania i wątpliwości
Choć przegląd naszych praktyk dotyczących bezpieczeństwa zapewnił szeroki obraz naszego podejścia do tej kwestii, to z uwagi na złożoność tego obszaru i liczne działania podejmowane przez Atlassian w tym temacie nie jesteśmy w stanie opisać tutaj szczegółowo każdego aspektu.
Jeśli potrzebujesz więcej informacji, możesz skontaktować się z zespołem Atlassian za pośrednictwem naszego portalu wsparcia lub zadać pytanie w naszej grupie Zaufanie i bezpieczeństwo w społeczności Atlassian.
Chcesz pogłębić swoją wiedzę?
Na tej stronie odnieśliśmy się do kilku innych dokumentów i zasobów. Zachęcamy, aby do nich sięgnąć. Pozwoli to lepiej zrozumieć nasze podejście do zaufania i bezpieczeństwa.