구성 관리
엔지니어링 팀이 구성 관리를 통해 견고하고 안정적인 시스템을 만드는 방법

Ian Buchanan
수석 솔루션 엔지니어
1950년대에 미국 국방부는 복잡한 시스템 개발의 변화를 추적하기 위한 기술 관리 방식을 개발했습니다. 2001년에 현재 구성 관리라고 부르는 기술 관리 시스템에 관한 통합 가이드북을 발표하기 전까지 이 시스템과 다양한 반복은 매우 기술적인 이름으로 불렸습니다. 오늘날 구성 관리는 국방부뿐만 아니라 소프트웨어 개발, IT 서비스 관리, 토목 엔지니어링, 산업 엔지니어링 부문 등에서 사용되고 있습니다.
구성 관리란 무엇입니까?
구성 관리는 제품 수명 주기 동안 제품 특성의 일관성을 유지하기 위한 시스템 엔지니어링 프로세스입니다. 기술 분야에서 구성 관리는 IT 시스템의 개별 구성 항목을 추적하는 IT 관리 프로세스를 의미합니다. IT 시스템은 세부적으로 다양한 IT 자산으로 구성됩니다. IT 자산에는 소프트웨어, 서버 또는 서버 클러스터 등이 있습니다. 다음에서는 IT 소프트웨어 자산 및 소프트웨어 자산 CI/CD에 직접 적용되는 구성 관리를 집중적으로 살펴봅니다.
소프트웨어 구성 관리는 소프트웨어 시스템 구성 메타데이터의 변경 사항을 추적하고 모니터링하는 시스템 엔지니어링 프로세스입니다. 소프트웨어 개발 분야에서 구성 관리는 일반적으로 버전 제어 및 CI/CD 인프라와 함께 사용됩니다. 이 게시물에서는 최신 애플리케이션과 애자일 CI/CD 소프트웨어 환경에서의 사용 방식을 집중적으로 살펴봅니다.
구성 관리가 중요한 이유는 무엇입니까?
관련 자료
마이크로서비스와 모놀리식 아키텍처 비교
솔루션 보기
Compass를 사용하여 구성 요소 관리
구성 관리를 통해 엔지니어링 팀은 구성 데이터에 대한 업데이트를 자동으로 관리 및 모니터링하는 도구를 사용하여 강력하고 안정적인 시스템을 구축할 수 있습니다. 복잡한 소프트웨어 시스템은 크기와 복잡성이 다른 컴포넌트로 구성됩니다. 구체적으로 마이크로서비스 아키텍처를 예로 들 수 있습니다. 마이크로서비스 아키텍처의 각 서비스는 구성 메타데이터를 사용하여 자체적으로 등록하고 초기화합니다. 소프트웨어 구성 메타데이터의 예는 다음과 같습니다.
- CPU, RAM 등을 위한 컴퓨팅 하드웨어 리소스 할당 사양
- 다른 서비스, 데이터베이스 또는 도메인에 대한 외부 연결을 하는 엔드포인트
- 비밀번호 및 암호화 키와 같은 비밀 데이터
위와 같은 구성 값은 우선 순위에서 밀리기 쉽기 때문에 정리되지 않거나 분산되는 경우가 많습니다. 비밀번호와 URL이 적힌 수많은 포스트잇이 사무실 주변에서 날아다닌다고 상상해 보세요. 구성 관리는 구성을 위한 중앙 위치에 “단일 정보 출처”를 만들어 이러한 문제를 해결합니다.
Git은 구성 데이터를 관리하기 위한 유용한 플랫폼입니다. 구성 데이터를 Git 리포지토리로 이동하면 버전 제어를 이용할 수 있으며, Git 리포지토리를 단일 정보 출처로 이용할 수 있습니다. 버전 제어는 예기치 않게 문제를 일으키는 변경 사항과 같은 또 다른 구성 문제도 해결합니다. 코드 검토 및 버전 제어를 사용하여 예기치 않은 변경 사항을 관리하면 가동 중지 시간을 최소화하는 데 도움이 됩니다.
구성 값은 대개 추가, 제거 또는 수정하게 됩니다. 버전 제어가 없으면 문제가 발생할 수 있습니다. 한 팀원이 소프트웨어가 개인용 노트북에서 더 효율적으로 실행되도록 하기 위해 하드웨어 할당 값을 조정할 수 있습니다. 나중에 소프트웨어를 프로덕션 환경에 배포할 때 새로운 구성이 부적절한 영향을 미치거나 중단을 일으킬 수 있습니다.
버전 제어 및 구성 관리는 구성 수정 사항에 대한 강력한 가시성을 제공하여 문제를 해결합니다. 구성 데이터가 변경되면 버전 제어 시스템이 이를 추적하므로, 팀원은 수정 사항에 대한 감사 추적을 검토할 수 있습니다.
구성 버전 제어를 통해 구성의 롤백 또는 “실행 취소”가 가능하므로 예기치 않은 중단을 방지할 수 있습니다. 구성 버전 제어를 이용하면 마지막으로 알려진 안정 상태로 빠르게 되돌릴 수 있습니다.
구성 관리가 DevOps, CI/CD 및 애자일에 적합한 이유
구성 데이터는 지금껏 관리할 대상이 아니었기 때문에 우선 순위에서 밀리기 쉽습니다. 실제 코드가 아니기 때문에 즉시 버전 제어로 관리되지 않습니다. 그리고 최상위 데이터가 아니기 때문에 기본 데이터베이스에 저장되지 않습니다. 기존의 소규모 시스템 관리는 일반적으로 스크립트 및 임시 프로세스 컬렉션을 사용하여 수행됩니다. 구성 데이터는 간과될 수 있지만 시스템 운영에는 매우 중요합니다.
클라우드 인프라가 등장하면서 새로운 인프라 관리 패턴이 개발되고 채택되었습니다. 클라우드 기반의 복잡한 시스템 아키텍처는 구성 데이터 파일을 사용하여 관리 및 배포됩니다. 새로운 클라우드 플랫폼을 통해 팀은 YAML과 같이 사람과 기계가 읽을 수 있는 데이터 파일을 통해 프로비저닝해야 하는 네트워크 연결과 하드웨어 리소스를 지정할 수 있습니다. 그런 다음 데이터 파일을 읽고 인프라를 클라우드에서 프로비저닝합니다. 이 패턴을 IaC(코드형 인프라)라고 합니다.
DevOps 구성 관리
인터넷 애플리케이션 개발 초기에는 하드웨어 리소스와 시스템 관리가 주로 수동으로 이뤄졌습니다. 시스템 관리자는 구성 데이터를 기반으로 하드웨어 리소스를 수동으로 프로비저닝하고 관리하면서 구성 데이터를 관리했습니다.
구성 관리는 DevOps 수명 주기의 핵심 부분입니다. DevOps 구성은 시스템 관리 역할이 진화 및 자동화된 것으로, 인프라 관리 및 배포를 자동화합니다.
또한 DevOps 구성은 소프트웨어 엔지니어가 시스템 관리를 할 수 있도록 지원합니다. 오늘날 기업은 이를 활용하여 소프트웨어 엔지니어가 온디맨드 방식으로 필요한 리소스를 요청하고 프로비저닝할 수 있도록 돕습니다. 따라서 소프트웨어 개발 팀이 별도의 시스템 관리 팀의 리소스를 기다리는 동안 발생할 수 있는 조직 종속성 병목 현상이 사라집니다.
CI/CD 구성 관리
CI/CD 구성 관리는 풀리퀘스트 기반 코드 검토 워크플로를 활용하여 라이브 소프트웨어 시스템에 대한 코드 변경 배포를 자동화합니다. 동일한 워크플로를 구성 변경에도 적용할 수 있습니다. 구성 변경 요청이 승인되면 실행 중인 시스템에 즉시 배포하도록 CI/CD를 설정할 수 있습니다. 이 프로세스의 완벽한 예는 GitOps 워크플로입니다.
애자일 구성 관리
구성 관리를 통해 애자일 팀은 구성 작업을 명확하게 분류하고 우선 순위를 지정할 수 있습니다. 구성 작업의 예로는 다음과 같은 번거로운 작업이 있습니다.
- 프로덕션 SSL 인증서 업데이트
- 새 데이터베이스 엔드포인트 추가
- 개발, 스테이징 및 프로덕션 이메일 서비스의 비밀번호 변경
- 새로운 타사 통합을 위한 API 키 추가
팀은 구성 관리 플랫폼을 이용해 구성 작업에 필요한 작업을 보고 파악할 수 있습니다. 구성 관리 작업은 다른 작업에 대한 종속성으로 식별할 수 있으며, 애자일 스프린트를 통해 적절하게 처리할 수 있습니다.
구성 관리 도구
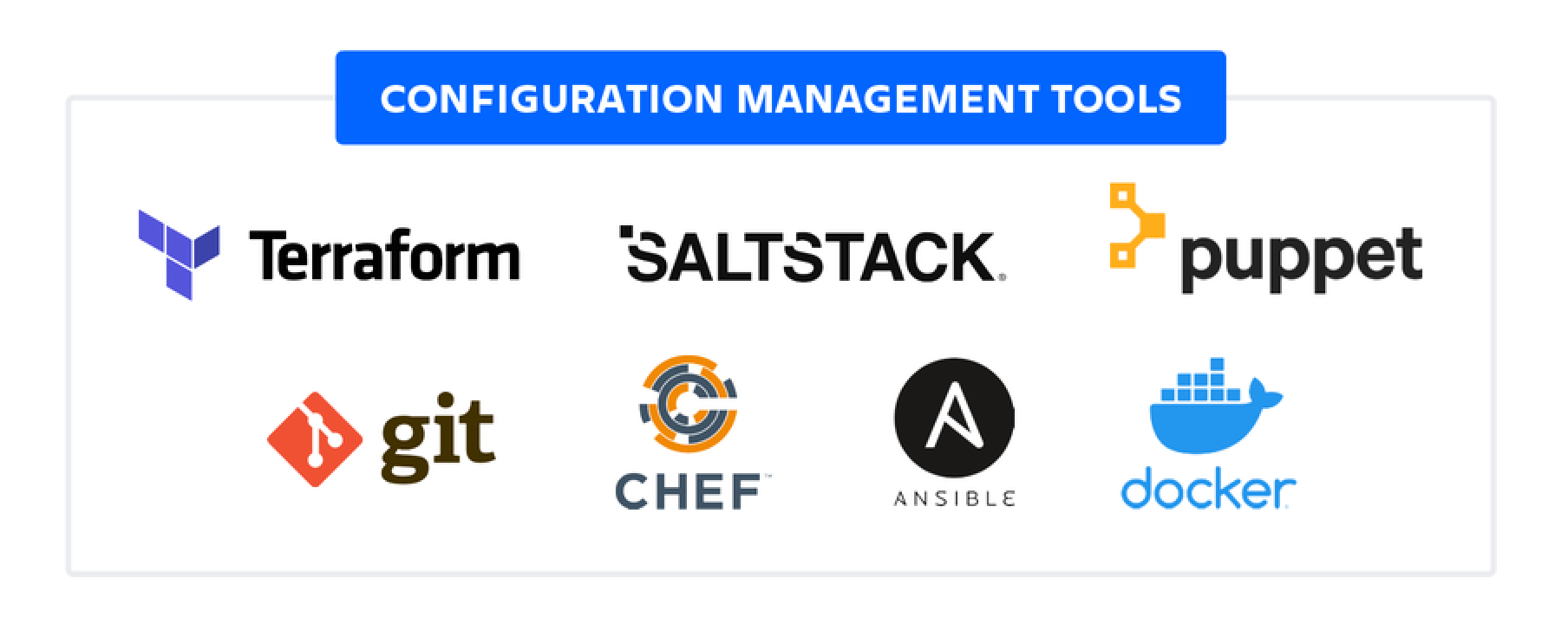
Git
Git은 코드 변경 사항을 추적하는 업계 최고의 버전 제어 시스템입니다. Git 리포지토리에 코드와 함께 구성 관리 데이터를 추가하면 전체 프로젝트에 대한 종합적인 버전 제어를 확인할 수 있습니다. Git은 상위 수준의 구성 관리를 지원하는 기본 도구입니다. 다음의 기타 구성 관리 도구는 Git 리포지토리에 저장되고 Git 버전 제어 추적을 활용할 수 있습니다.
Docker
Docker는 구성 잠금과 같은 고급 구성 관리 형태인 컨테이너화를 도입했습니다. Docker는 Dockerfiles라는 구성 파일을 기반으로 합니다. 이 파일은 운영 체제 상태의 예상 스냅샷을 재구성할 때 실행되는 명령 목록을 포함합니다. Docker는 사전 구성된 애플리케이션의 스냅샷인 이 Dockerfile로부터 컨테이너를 만듭니다. Dockerfiles는 버전 추적을 위해 Git 리포지토리에 커밋되며, 인프라에 배포하기 위해서는 추가 구성 관리가 필요합니다.
Terraform
Terraform은 HasiCorp의 오픈 소스 구성 관리 플랫폼입니다. Terraform은 IaC를 사용하여 클러스터, 클라우드 인프라 또는 서비스를 프로비저닝하고 관리합니다. Terraform은 Amazon Web Services(AWS), Microsoft Azure 및 기타 클라우드 플랫폼을 지원합니다. 각 클라우드 플랫폼에는 서버, 데이터베이스 및 큐 같은 공통 인프라 컴포넌트에 대한 자체 표시 및 인터페이스가 있습니다. Terraform에는 클라우드 플랫폼을 위한 구성 도구의 추상화 계층이 있어 팀이 재현 가능한 인프라 정의로 구성된 파일을 작성할 수 있도록 지원합니다.
Ansible, Salt Stack, Chef, Puppet
Ansible, Salt Stack, Chef, Puppet은 IT 자동화 프레임워크로, 시스템 관리자의 많은 기존 프로세스를 자동화합니다. 각 프레임워크는 실행 파일로 실행되는 일련의 구성 데이터 파일(일반적으로 YAML 또는 XML)을 사용합니다.
구성 데이터 파일은 시스템을 구성하기 위해 수행할 일련의 작업을 지정합니다. 그런 다음 실행 파일을 통해 작업을 실행합니다. 실행 파일은 시스템마다 언어가 다릅니다. Ansible과 Salt Stack은 Python 기반이고 Chef는 Ruby 기반입니다. 이 워크플로는 애드혹 셸 스크립트 실행과 유사하지만, 각 플랫폼 에코시스템을 통해 보다 체계적이고 개선된 환경을 제공합니다. 이 도구는 CI/CD를 달성하는 데 필요한 자동화를 지원합니다.
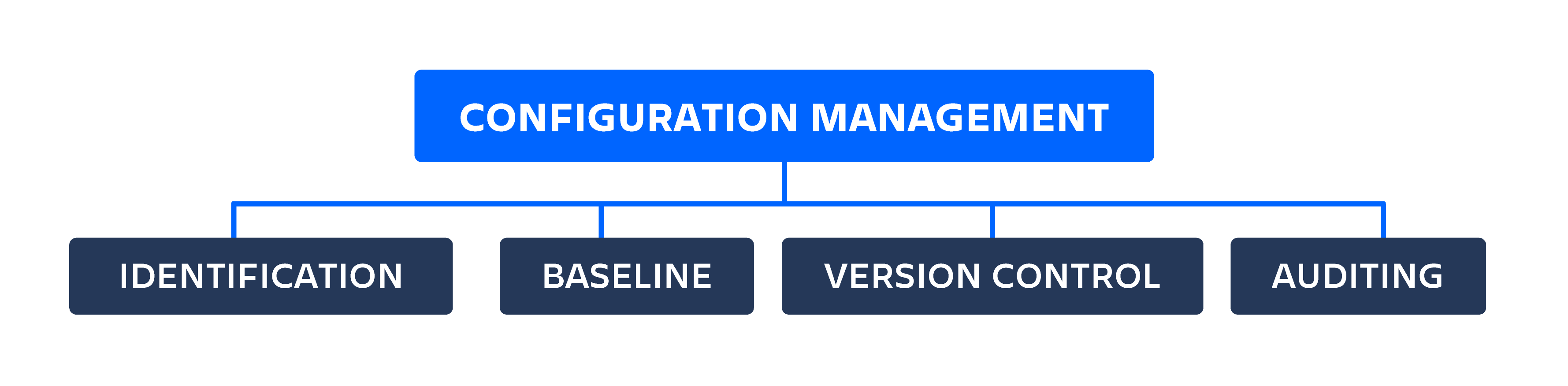
구성 관리를 구현하는 방법
식별
구성 관리를 위한 첫 번째 작업은 정보 수집입니다. 서로 다른 애플리케이션 환경, 개발, 스테이징 및 프로덕션에서 사용 중인 모든 컴포넌트 및 서비스에 대해 구성 데이터를 집계하고 컴파일해야 합니다. 비밀번호 및 키와 같은 모든 비밀 데이터를 식별하고 안전하게 암호화 및 저장해야 합니다. 여기서 구성 데이터를 데이터 파일로 구성해 중앙 정보 출처로 지정할 수 있어야 합니다.
기준선
구성 데이터를 집계하고 구성한 후 기준선을 설정할 수 있습니다. 기준선 구성은 알려진 구성 상태로, 종속 소프트웨어를 오류 없이 성공적으로 작동해 줍니다. 기준선은 일반적으로 작동하는 프로덕션 환경의 구성을 검토하고 해당 구성 설정을 커밋하여 만듭니다.
버전 제어
개발 프로젝트는 버전 제어 시스템을 사용해야 합니다. 버전 제어 시스템이 없다면 Git을 설치하고 프로젝트의 리포지토리를 초기화한 다음 구성 데이터 파일을 리포지토리에 추가하세요. 리포지토리 구성 데이터를 추가하기 전에 비밀번호나 키와 같은 비밀 데이터가 외부 키로 암호화되었는지 꼭 확인하세요. 비밀 데이터가 실수로 리포지토리에 커밋되면 엄청난 위험이 따릅니다. 리포지토리 기록에서 제거해야 합니다. 그렇지 않으면 악용될 위험이 있습니다.
감사중
구성 데이터를 구성하고 리포지토리에 추가하면, 시스템 구성을 공동 작업하고 이에 대한 가시성을 확보할 수 있습니다. 그런 다음 소프트웨어 팀이 코드를 검토하고 편집하는 데 사용하는 인기 있는 풀리퀘스트 워크플로를 구성 데이터 파일에 적용할 수 있습니다. 이러한 방식으로 감사 및 회계 시스템을 만들 수 있습니다. 구성에 적용된 모든 변경 사항은 팀에서 검토하고 수락해야 합니다. 이를 통해 구성 변경에 대한 책임감과 가시성을 추가로 확보할 수 있습니다.
IT 운영 및 CMDB
지금까지 애자일 및 CI/CD 환경의 소프트웨어 자산에 적용되는 구성 관리에 대해 논의해 보았습니다. IT 운영 팀 또한 적극적으로 구성을 관리하고 있으며 이는 구성 관리 데이터베이스(CMDB)에서도 마찬가지입니다. CMDB는 하드웨어, 소프트웨어 및 네트워크 구성 요소 정보를 비롯해 이들 간의 관계에 대한 정보를 저장합니다. IT 운영 팀은 상호 의존성, 라이선스, 계약 그리고 모든 것이 원활하게 돌아가도록 하는 데 필요한 서비스 및 예산을 고려합니다. 상호 의존성을 관리하는 IT 운영 팀과 구성을 코드로 관리하는 소프트웨어 팀을 갖춘 조직은 안정적인 시스템과 뛰어난 가동 시간을 누릴 수 있습니다.
결론...
구성 관리는 복잡한 소프트웨어 시스템을 관리하는 데 필요한 도구입니다. 구성 관리가 결여되면 안정성, 가동 시간 및 시스템 확장성에 심각한 문제가 발생할 수 있습니다. 현재 많은 소프트웨어 개발 도구에는 구성 관리 기능이 내장되어 있습니다. Bitbucket은 Git 풀리퀘스트 워크플로 및 CI/CD 파이프라인을 중심으로 하는 강력한 구성 관리 시스템을 제공합니다.
이 문서 공유
다음 토픽
여러분께 도움을 드릴 자료를 추천합니다.
이러한 리소스에 책갈피를 지정하여 DevOps 팀의 유형에 대해 알아보거나 Atlassian에서 DevOps에 대한 지속적인 업데이트를 확인하세요.

Compass 커뮤니티

자습서: 컴포넌트 만들기