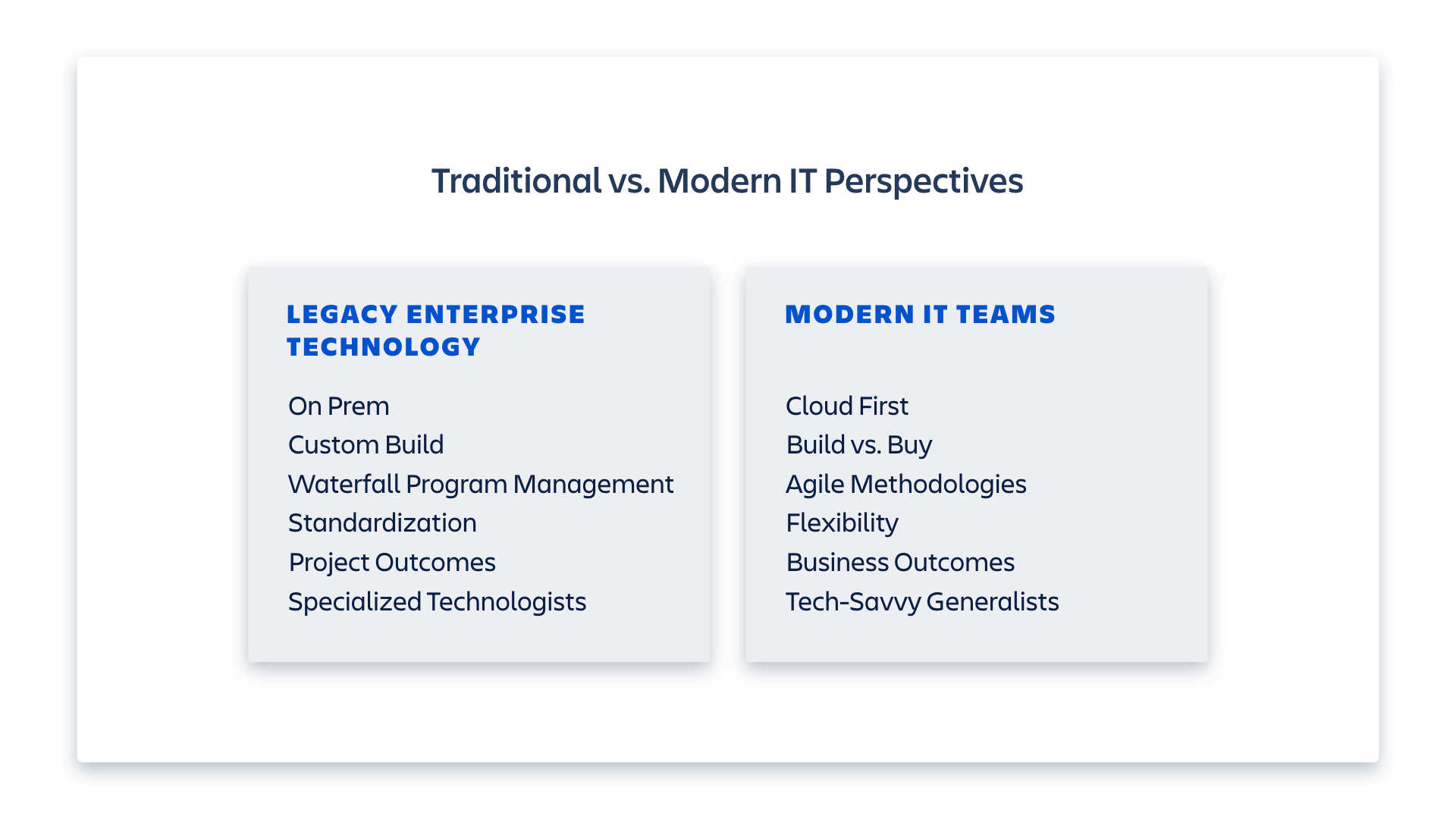
“Shadow IT” can be a divisive subject depending on how long you’ve been in the IT field. There is a legacy attitude within many IT teams that shadow IT must be controlled – but it can bring significant benefits to an organization. Modern IT teams understand these benefits, and focus on balancing shadow IT’s value and risk.
Moving past that legacy attitude and developing a modern IT mentality in your organization can be difficult. It helps to understand where that control-first attitude came from in the first place.
A brief history of shadow IT
Legacy IT teams custom-built and maintained on-premise technology, which was expensive to build and expensive to run. It took months, sometimes even years, to deliver. It was difficult to change a system once it was built, despite the fact that those systems rarely met business expectations.
When those systems were delivered, the business partners for whom they were built often took one look at the situation – they were footing the bill for a project that wouldn’t meet their needs, while waiting months for it to be researched, built and delivered – and came to a “better” solution: We’ll build it and maintain it ourselves – we just won’t tell IT!
Anyone who has been in IT for more than a minute has heard the stories. During my own time in IT, I’ve heard some good ones:
- An HR team stored thousands of personnel files on an unprotected, unregistered server under the desk of one of the managers. Aside from concerns about storing personally identifiable information (PII), there was no backup solution if that server were to crash.
- A company discovered 47 instances of the same customer relationship management (CRM) software. I can only imagine the cost and vendor management efficiencies they gained when they consolidated.
- A sales ops team stored important data with an unregistered, third-party vendor, which then ended up going into bankruptcy. All the files and data were locked up in bankruptcy court for years.
Obviously, the DIY approach can open a company up to risk in a number of ways. And when things go wrong, guess who gets called in to clean up the mess? That’s right: the IT team.
It’s not hard to see how a team’s desire to build a “better” tool in the shadows – even if the intentions were good – evolved into an adversarial relationship between that business unit and IT. It also helps explain a misconception that continues to this day: that IT just wants to take control or shut down unsanctioned tools.
Visibility is key
While there are legitimate situations in which controlling or shutting down a technology makes sense, it’s wrong to assume that all IT teams are the control-hungry, “no and slow” teams their reputation suggests.
Modern IT teams must operate differently, and with a collaborative mindset. They need to focus on delivering business results and on working closely with their tech-savvy business partners. Thanks to the proliferation of cloud-based solutions (including SaaS) and new methodologies (like agile) for working collaboratively, IT can lower the barrier to entry for new tools, move quickly, and adapt as needed. They must also understand that shadow IT is a great opportunity to experiment with new tools and succeed (or fail!) quickly, with one caveat: IT needs visibility.
It’s important to understand that this need for visibility isn’t so IT can shut down new tools. Visibility allows IT to categorize each technology, quantify its importance to the business, analyze risk, and determine how to support it (or let it run free).
Taking a spectrum-based view of shadow IT
In the legacy IT days, IT either managed an enterprise tool, or they didn’t; they took a binary view of the technology of an organization. Today, modern IT teams can take a spectrum-based view of the tech landscape, illustrated by the diagram below.
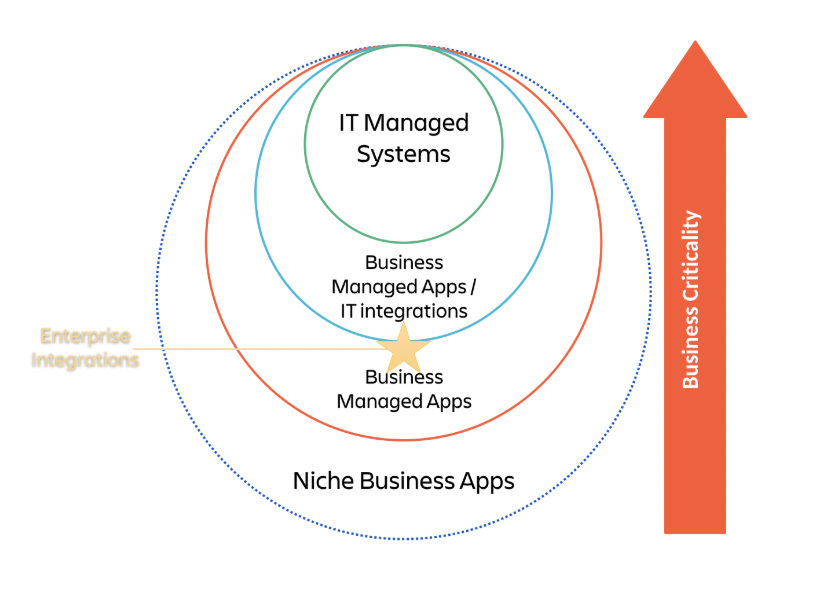
In this view, IT still maintains the core systems that run an enterprise. Those platforms drive critical business processes: customer relationship management (CRM), human capital management (HCM), enterprise resource planning (ERP), and more. But with advances in integration, along with the availability of SaaS solutions, IT can maintain access to core systems while allowing data to pass to business-managed apps.
This model accepts that some apps just don’t need to be managed by IT, especially if these apps have no need to integrate, or don’t contain critical data or support core business processes. Many apps used by modern teams have a short shelf life, either because they’re used only for certain events or because teams only want to try or test it. In this case, shadow IT apps have a great opportunity to prove out business value without involving IT (other than giving them a heads up, of course).
Modern IT embraces even niche business apps (the outer circle in the chart) because:
- Cloud apps foster innovation via experimentation: With the proliferation of cloud apps, freemium models to encourage a try-before-you-buy approach, and the ease of getting started, business teams can explore and test different tools before committing to them. This is critical for moving quickly to drive innovation.
- Cloud apps can be deployed rapidly: These days, products are built with ease of getting started and quick deployment in mind. What used to take months of custom app development by the IT team is now a simple task of adding users to an app being tested (see above) or a click-buy-deploy process that can be done in a matter of minutes.
- Modern tools often have a lower total cost of ownership (TCO): SaaS often offers a lower TCO than a custom-built or on-prem app because it doesn’t require IT build costs, hosting needs, or ongoing support. These services are packaged into the SaaS solution and are often much more economical – especially considering the niche nature of apps in this outer circle – than the alternative of having IT build and manage them.
As I mentioned above, modern IT teams don’t exist to control or shut your apps down. They just need visibility. Even if IT doesn’t choose to have high engagement – as in the case of niche business apps – visibility is key for all levels of the spectrum:
- It helps IT understand what capabilities their teams are using, so if critical mass is reached, they can centralize this capability at the enterprise level if needed.
- It provides insight into how data is being used and shared, and whether the data needs to be moved to a controlled or governed system.
- It can reduce cost if duplicative capabilities are being purchased by different teams across the company.
- It allows IT to categorize each application into the appropriate level, and understand whether they need to manage it or leave it alone.
The new rules of shadow IT
There are a few things to keep in mind when reviewing your shadow IT footprint. Start by looking at the chart above illustrating the spectrum-based view, and determining what to include and exclude from each circle. Consider the following when determining where your tools fall in the circles:
- Governance/Compliance Regulations: Is this tool part of core company processes and in need of high availability or controlled access? Is it part of a financial process, and relevant to regulations such as SOX?
- Integrations: How integrated is the application with other technologies or apps in your architecture?
- Operations and Availability (uptime/downtime): Is this tool needed 24/7? What type of support or SLAs does the business have in place that could be impacted by this tool?
- Data Usage: What other tools or teams are the upstream and downstream consumers of the data? Do any of the data fall under privacy policies like GDPR?
After placing your tools in their appropriate circles, consider how data and applications could move between the circles:
- Change: What is the rate and complexity of change within the context of your business? As complexity increases, items may need to move from business team control to IT control.
- Scale: What are the upstream and downstream dependencies for these tools to scale?
- TCO: How is TCO impacted as tools move circles or change ownership?
While I don’t expect you to convince your company to magically embrace a new approach to Shadow IT overnight, there are some resources your IT team can embrace today that will be helpful on any shadow IT journey. The Atlassian Team Playbook is a free resource for everyone, and can be valuable for IT teams. I recommend taking a look at the following elements:
- IT Project Poster: A great way to get teams on the same page (literally!) when defining a project.
- Change Management Kick-off: Helps teams think through the impact of their changes, including who is most likely to be affected, and how to help them navigate through the change.
- Stakeholder Communications: IT professionals cannot over-communicate. This play helps IT think through who is a stakeholder and how to best communicate with them.
- End-to-End Demo: Process mapping but in a lightweight, friendly way that helps bridge the conversation between a business team’s process and the technical solution.
Change is hard for just about any company, and almost always involves IT. But with the right frameworks and a focus on collaboration, you can make it easier.








